OSINT Field Notes #7
Fitness Trackers, Shadow Fleet, Satellite Blackouts and How To Investigate With Strava
Welcome to edition seven of OSINT Field Notes.
The past month has been active. A French sailor’s morning jog around an aircraft carrier deck handed researchers the exact position of the Charles de Gaulle in the eastern Mediterranean. Within weeks, the i Paper had found 519 British service personnel, including nuclear submarine crews, publicly logging runs inside facilities that are supposed to be a bit more private. Same story, same app, different locations.
Away from fitness trackers, the month produced one of the most methodologically rich investigations of the year: OCCRP placing Wagner-linked and GRU-linked operatives aboard Russia’s sanctioned Baltic tanker fleet, using crew manifests, a leaked mercenary registry, and border crossing data in combination. That’s the Case File this month, and it’s worth digging into, not just for what was found, but for how the data sources were layered to make the findings.
The Technical Teardown goes deep on Strava: not as a one-off news story, but as a standing data and research platform with distinct access methods useful across conflict documentation, due diligence, fraud investigation, and corporate research. It’s also a lesson on privacy, especially for those of you, like me, who like to share your outdoor runs with friends.
If you’re finding value in this newsletter, the back catalogue (editions 1–6) is now available exclusively to paid subscribers. Each new edition stays free. That won’t change. But paid subscriptions help me keep producing this work and give you access to the full archive. You can upgrade on the OSINT Field Notes Substack page.
Ben.
1. DISPATCHES
Strava betrays the Charles de Gaulle, again
On March 13, a French Navy officer logged a run of just over 7km on his public Strava profile and inadvertently broadcast the real-time position of France’s only nuclear-powered aircraft carrier, near Cyprus. Le Monde reported the location a short time later. It is the same failure eight years on from the 2018 heatmap scandal and Le Monde’s 2024 #StravaLeaks series exposing Macron’s security detail, so treat Strava as a standing intelligence source, not a one-off curiosity. Le Monde | The Independent | TechCrunch
Investigator takeaway: Strava’s default is public. Every new exposure confirms the same structural vulnerability: account-level privacy settings that most users never change.
i Paper: 519 UK military personnel exposed at sensitive bases via Strava
In three months of public Strava data from January 2026, the i Paper identified 519 military staff, contractors, and family members logging runs inside restricted areas at HMNB Clyde (Trident nuclear base), RAF Akrotiri, Diego Garcia, Menwith Hill, Fylingdales, and Northwood. The i Paper
Investigator takeaway: Systematic site-by-site segment analysis is a replicable method. The i Paper’s approach: bounding a known facility, pulling all public segments within it, then identifying runners from leaderboards, is documented well enough to apply elsewhere.
Planet Labs imposes a 14-day imagery blackout over the Middle East
Planet Labs initially imposed a 96-hour delay on new Middle East imagery from March 10, citing risk of tactical misuse, then extended it to 14 days. Vantor (formerly Maxar) applied similar access controls. Since then, the situation has escalated further: Planet announced an indefinite managed-access model at the US government’s request, retroactive to March 9, with imagery released only on a case-by-case basis.
This is one of the most significant commercial satellite access restrictions during active conflict, and it directly affects conflict damage assessment and independent monitoring. If your workflow relies on a single commercial optical provider, build in Sentinel-1 SAR as a free, government-operated fallback before you need it — it works through cloud cover and is operated by ESA, not a company subject to US commercial or political pressure.
Investigator takeaway: Provider diversification is now an operational requirement, not a nice-to-have. Free Sentinel-2 optical and Sentinel-1 SAR data from ESA’s Copernicus programme should be part of any monitoring baseline. There are many other publicly available satellite imagery and geospatial data platforms that support conflict monitoring, you can find six top satellite sources in a YouTube tutorial I made here.
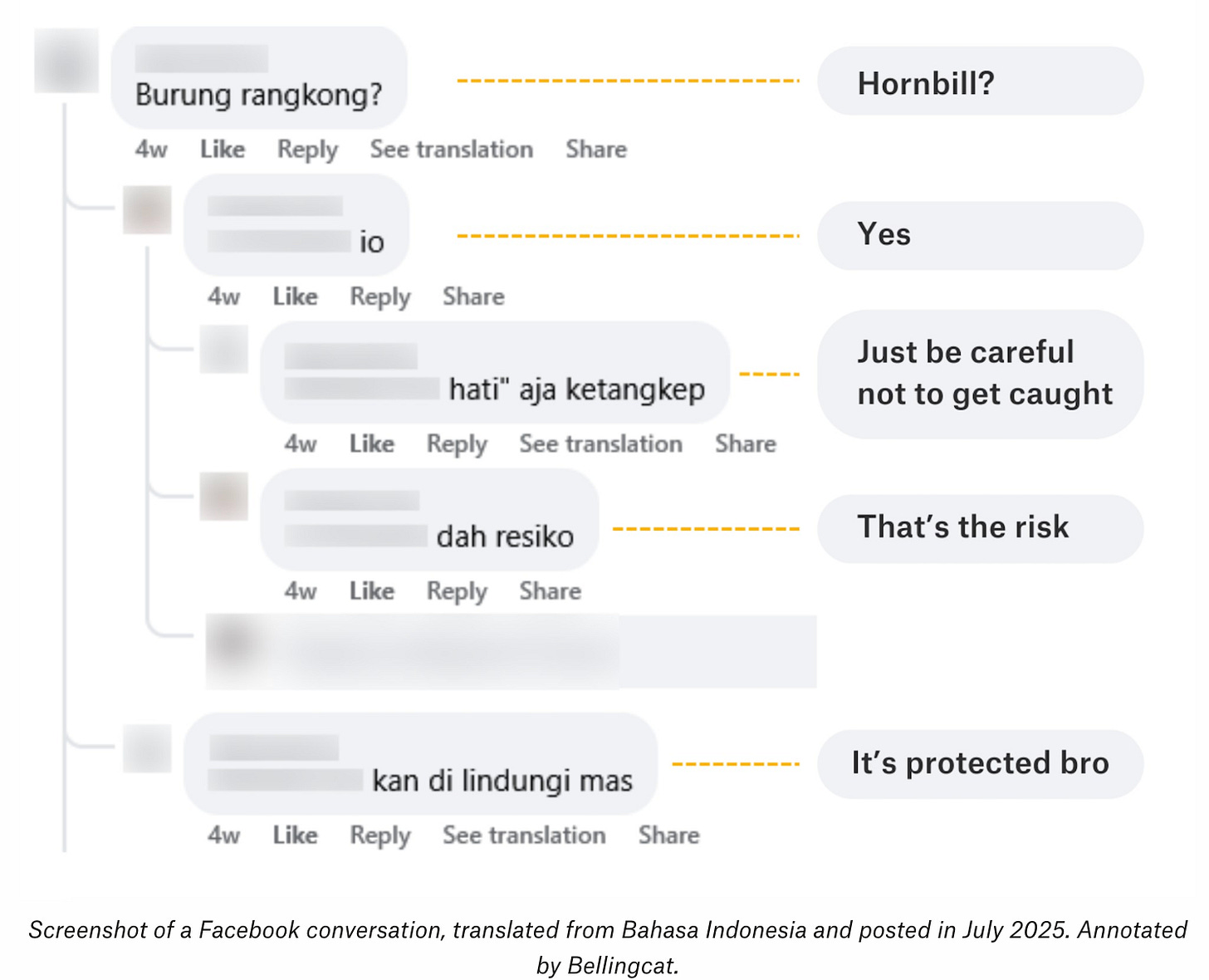
Bellingcat traces Indonesian wildlife trafficking to a single Jakarta broker
Nine Facebook groups with 70,000+ members traded IUCN-listed species using coded pricing (A = Rp100,000; “WC” for wild-caught). Bellingcat traced six profiles back to one broker, identifying a pet shop called Station Sato in the Jakarta suburb of Cibinong through product photos that matched the physical location. Mongabay then visited the shop undercover, confirming the connection. The coded-pricing system and “wa.” shorthand (pasted before WhatsApp numbers) used by sellers in these groups is a pattern found across illicit Facebook marketplaces, not just wildlife trade. Bellingcat | Mongabay
Investigator takeaway: Searching Facebook posts for industry terms (in this case “WC”) remains a reliable technique for extracting seller contact details from any illicit marketplace group.
OCCRP: Wagner and GRU operatives aboard Russia’s shadow fleet
OCCRP’s joint investigation identified 17 Russian men without maritime credentials on 20 sanctioned Baltic tanker voyages, 13 linked to Wagner, GRU, or paratroopers — cross-referenced against a leaked 2021 Wagner registry and border crossing records. This changes the analytical framing: Russia’s shadow fleet is no longer just a sanctions evasion story but a military deployment story, and that distinction matters for anyone monitoring Baltic maritime enforcement or modelling escalation risk. This is the Case File below. OCCRP
Meta’s H1 2026 Adversarial Threat Report
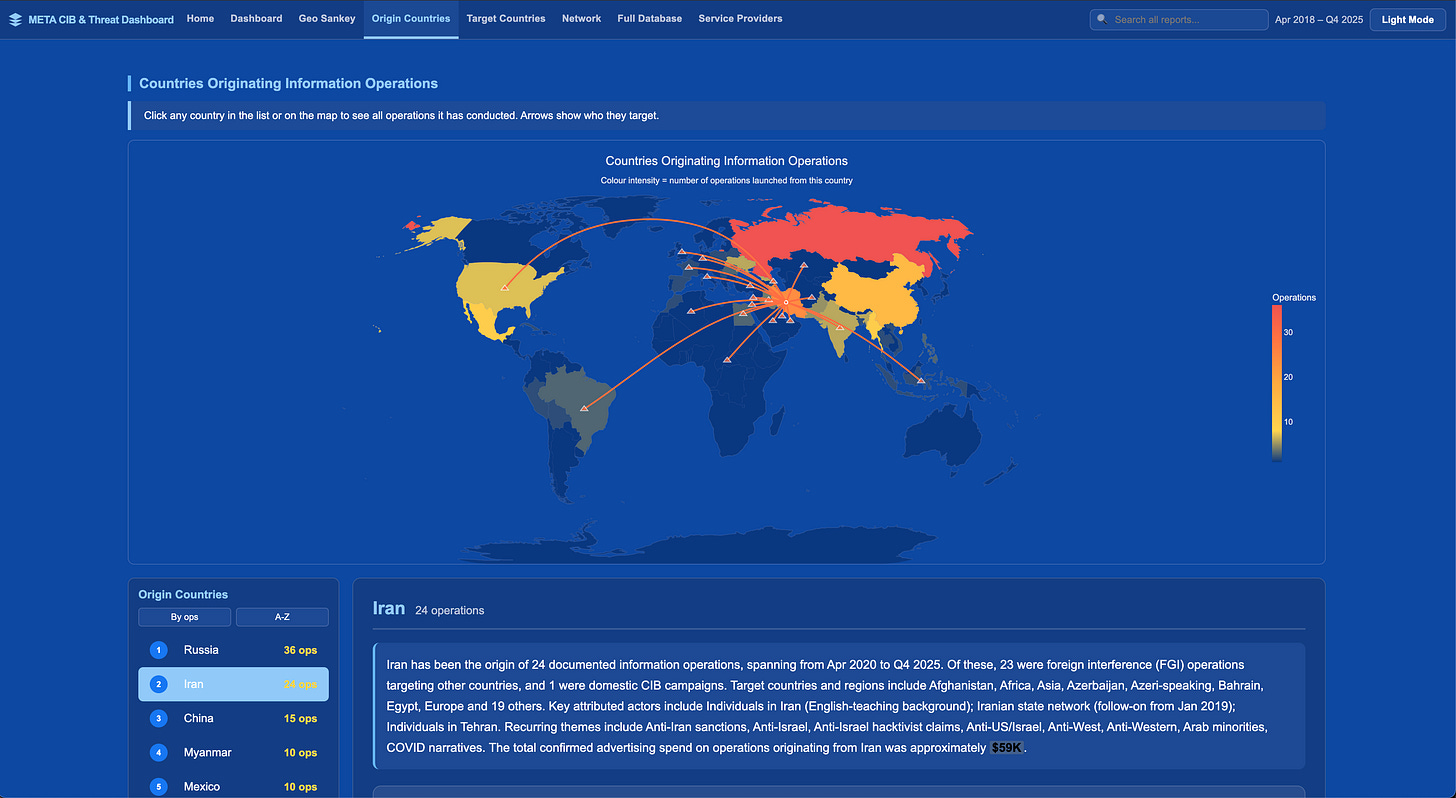
Meta’s semiannual adversarial threat report, published March 11, covers coordinated inauthentic behaviour, fraud and scams, nudify app networks, and cartel activity. The most practically useful section details an Iranian influence operation kill chain covering infrastructure setup, persona development, and amplification timing. The cartel section’s concept-driven discovery methodology for surfacing coded-language content is directly applicable to any investigation tracking illicit markets — read it alongside the wildlife trafficking dispatch above. Meta Transparency Centre
Investigator takeaway: Meta’s coded-language detection framework is transferable. If you’re investigating any marketplace using euphemisms or substitution codes, the methodology section describes a structured approach to identifying and mapping those patterns.
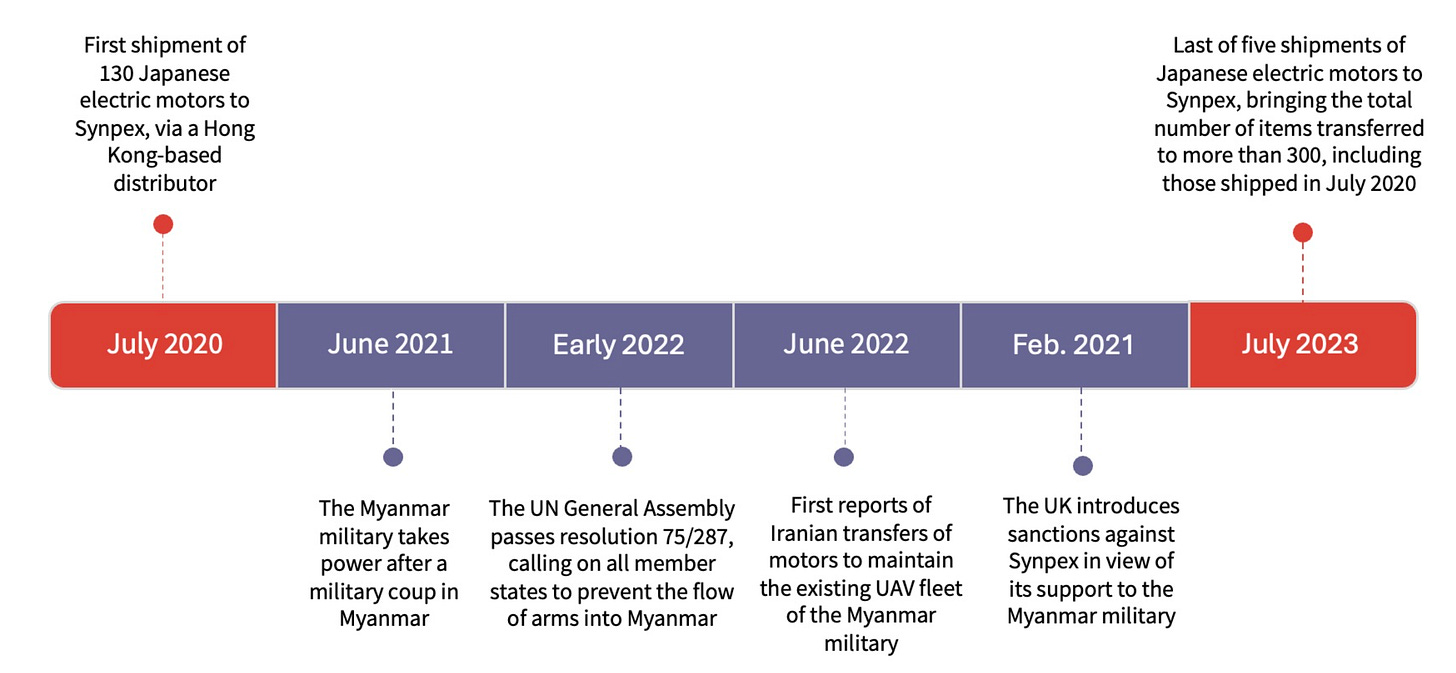
CAR traces Iranian drone motor to Myanmar via Chinese trademark records
Conflict Armament Research traced a Japanese electric motor from a recovered Iranian Sayyad-107 UAV through four countries: Japan → Hong Kong → Myanmar (Synpex) → Iran, identifying the Mahan Air connection through Chinese trademark registrations, which revealed that the same entity holds marks for both a sanctioned Iranian shipping company and the airline. CAR StoryMap
Investigator takeaway: Chinese trademark searches should be in your corporate investigation toolkit alongside standard registries. Shared registrant details across trademark filings can expose connections that ownership records alone won’t reveal. A good resource for this is CNIPA.
SIPRI Arms Transfers Database updated: global transfers up 9.2%
SIPRI’s arms transfers database covering 1950–2025 was updated March 9. Global transfers rose 9.2% between the 2016–20 and 2021–25 periods, the biggest increase since 2011–15, driven overwhelmingly by European demand, with states in Europe more than trebling their imports. US exports grew 27%, giving the US a 42% share of all global transfers. Russian arms exports fell sharply, continuing a steep decline. The US supplied 68% of Israel’s arms imports in the period. For any investigation touching arms supply chains, sanctions compliance, or conflict escalation, this is the primary open-source reference, freely queryable by supplier, recipient, weapon type, and year at armstransfers.sipri.org. SIPRI fact sheet (PDF)
Investigator takeaway: Bookmark the database. It’s free, covers 75 years of transfers, and is queryable at a granularity that no other public source matches.
The Londoner reveals real owners of 32,000 London properties via the Register of Overseas Entities
Using data compiled by Dan Neidle at Tax Policy Associates from the UK’s 2022 Register of Overseas Entities, The Londoner identified beneficial owners behind 32,611 London properties, including a Trump associate, a sanctioned Libyan wealth fund as landlord of the Oxford Street Harry Potter store, and 2,224 properties registered to one Jersey street. The ROE is now one of the most powerful UK beneficial ownership tools available to investigators and its underlying dataset has been made freely available by Tax Policy Associates. The Londoner
Investigator takeaway: The Tax Policy Associates dataset is downloadable and ready for your own analysis. If you work in property, corruption, or sanctions investigations touching the UK, this is primary source material.
CIB Dashboard: all of Meta’s coordinated inauthentic behaviour takedowns since 2017, visualised
An independent developer built a free interactive dashboard of every Meta CIB takedown since 2017, filterable by country, year, and actor — far more navigable than the raw transparency PDFs. Use it alongside Meta’s actual reports rather than instead of them. The developer flags important caveats: some attributions may be misleading (for example, a campaign attributed to Vietnam is likely a Middle East actor using Vietnamese infrastructure), and spend figures are not inflation-adjusted. CIB Dashboard
Investigator takeaway: Useful for quickly scoping which countries and actors have been disrupted by Meta and when, but always cross-reference against the primary reports for attribution detail.
Open Journalism: newsrooms are open-sourcing their investigative infrastructure
Scott Klein (ex-ProPublica) launched a fortnightly tracker of newsroom GitHub releases in March, 18 organisations published 21 repositories in the first two weeks, including MuckRock’s Klaxon change-detection extension, IRE’s investigative archive backend, and CBS News’ multi-collection document search tool built for the Epstein Files. Follow it as a low-noise signal for when funded newsrooms release datasets and infrastructure that can be repurposed without starting from scratch. openjournalism.news
2. TOOLKIT
DeadDrop: full-text Telegram search across 175M+ posts. Free tier launched March 9, indexing 175 million+ posts across 2 million+ Telegram channels with date-filtered keyword search; paid tiers cover historical data. Telegram has been one of the hardest platforms to search at scale without direct API access, and this fills that gap for tracking influence operations, extremist channels, and conflict communications. Link
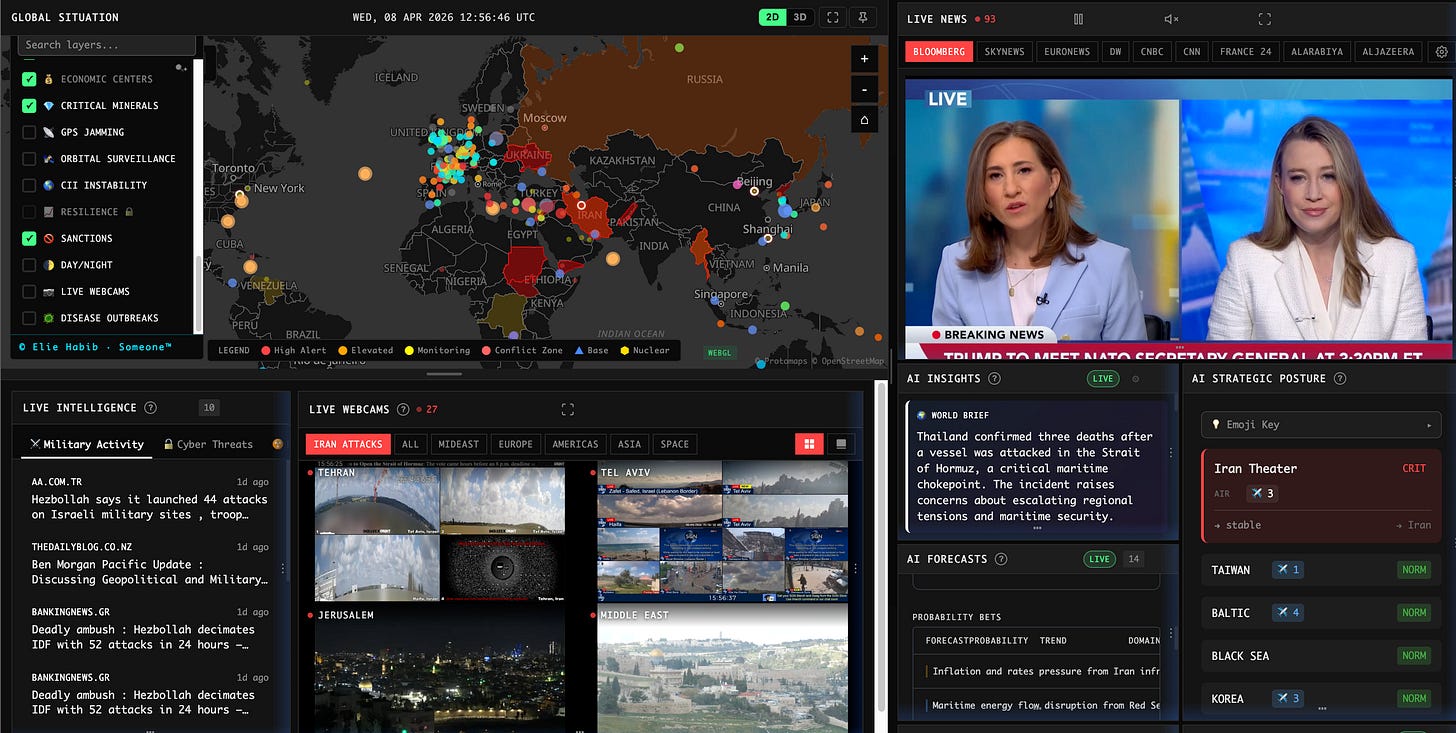
World Monitor: open-source real-time intelligence dashboard. Free, open-source, no login required. Aggregates 435+ feeds across news, financial markets, military movements (210+ bases, live ADS-B), cyber threats, and maritime chokepoints into a 3D globe with 45+ data layers, plus a Country Instability Index and local LLM support via Ollama. Watch-out: Data freshness varies significantly by layer. News is near-real-time, but some geopolitical risk scoring updates less frequently. Treat it as a triage and correlation tool rather than a primary source. Link | GitHub
OSINT Tools Library: investigation-focused tool directory from the OSINT Newsletter. A curated directory at tools.osintnewsletter.com. Tools are included because they have been used in real investigations, not just because they exist. Each entry covers use cases, access notes (free/paid/limitations), and links back to the newsletter issue where it was first documented, across sixteen categories from social media and geolocation to blockchain and network infrastructure. Link
Also worth your attention this month:
Bellingcat Turnstone: a historical ADS-B pattern search with dual-region flight connection queries, useful for tracing military air buildups or deportation flight routes. Access is restricted to journalists and academics by application, with self-hosting via GitHub for those with the technical setup.
Sat-Predict: solves the reverse overpass problem: predicting when a surface location will be scanned by a specific sensor rather than when the satellite is merely overhead. Directly useful given this month’s Planet Labs blackout.
SkyOSINT: real-time orbital tracking with manoeuvre detection and RF anomaly flagging, plus GPS jamming and spoofing threat layers. Most relevant if your work touches space domain awareness or conflict-area communications.
3. TECHNICAL TEARDOWN: RUN DATA
The dispatches above cover the headlines: a French officer’s run broadcasting the Charles de Gaulle’s position, and 519 UK military personnel logging activities inside restricted facilities.
Each time these stories surface, they’re covered as OPSEC failures. They are. But Strava is more than a source of military embarrassment, it’s a large, people-powered dataset with multiple distinct access methods, applicable well beyond conflict and national security.
Strava has over 180 million registered users across more than 190 countries. Insurance fraud investigators have used it to disprove disability claims such as a cyclist who claimed £60,000 for pain and suffering after a crash, but his public Strava runs and rides showed different). Corporate due diligence practitioners can use it to verify physical presence claims, identify workplace locations, and map professional networks. Human rights researchers can use it to place individuals at specific sites on specific dates. The military exposures are the headline cases, but the dataset is relevant any time physical movement, location, or capability is in question.
A note on access: many of Strava’s most useful research features have been progressively paywalled. The techniques below focus on what’s available for free, but if you’re conducting a serious investigation, a premium subscription opens up segment detail, full leaderboards, and historical activity data that the free tier no longer provides.
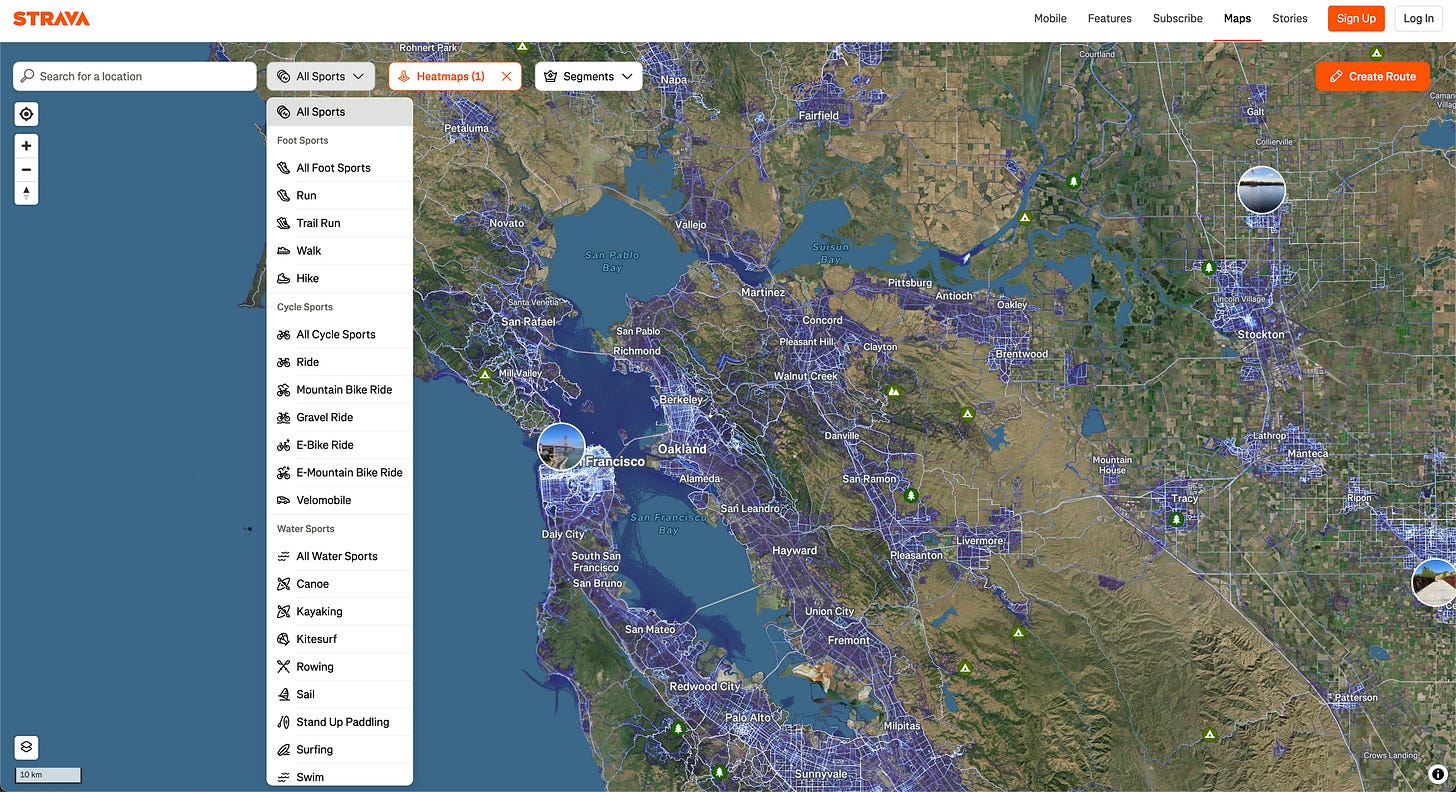
Technique 1: Heatmap analysis — locating facilities and routes
Strava publishes a global heatmap of aggregated activity data. Navigate to your area of interest and toggle between sport categories (running, cycling, kayaking). Bright clusters in unexpected locations (remote desert, forested areas, restricted zones) signal human presence worth investigating. Cross-reference against satellite imagery (Google Earth Pro, Sentinel Hub) to identify what’s there.
Look for linear bright lines inside facility perimeters, those are jogging or patrol routes. An installation that disappears from satellite imagery but stays bright on the heatmap confirms ongoing activity. The heatmap does not show individual users; it confirms presence at a location, not identity. Use it to scope where to look, then move to the Segment Explorer or profile search.
A good example of this is from 2018, where Nathan Ruser identified CIA compounds in Somalia, US bases in Syria and Iraq, British bases in the Falklands, and a lone cyclist circling Area 51. Bellingcat published the methodology guide and it remains largely current.
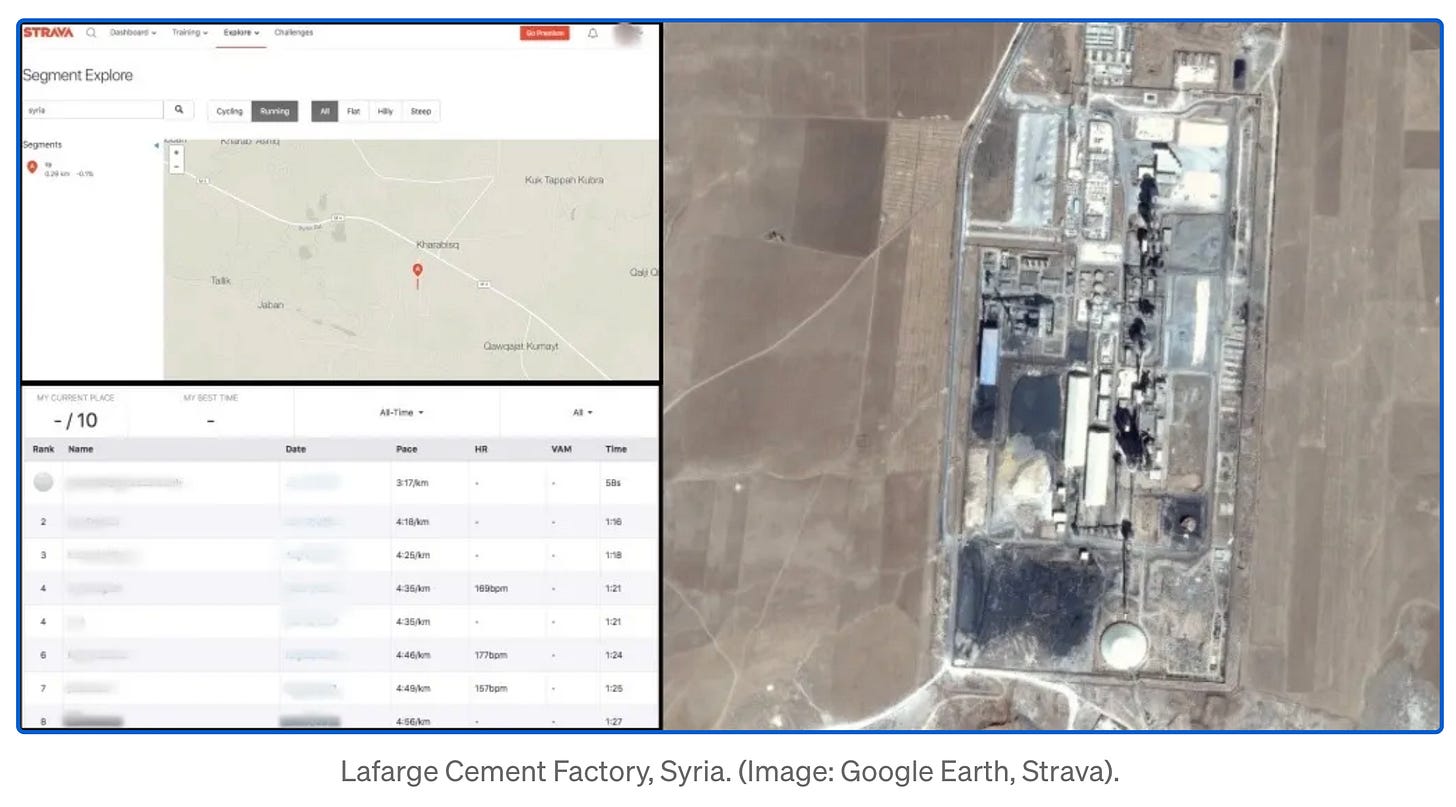
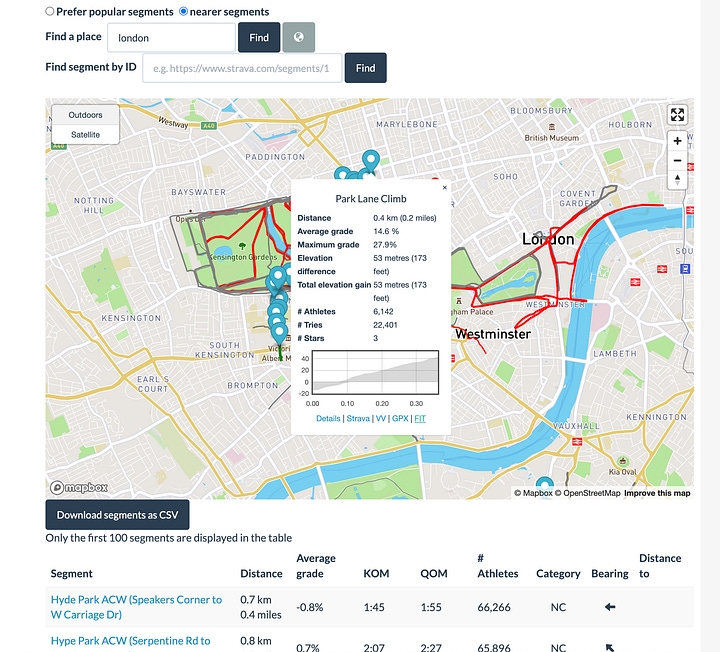
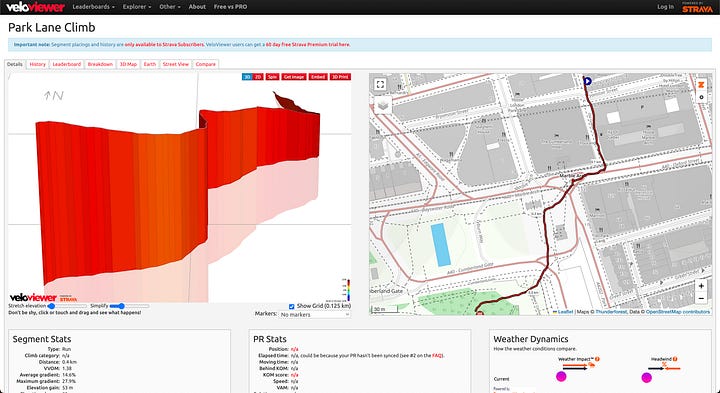
Technique 2: Segment Explorer — who runs where, and when
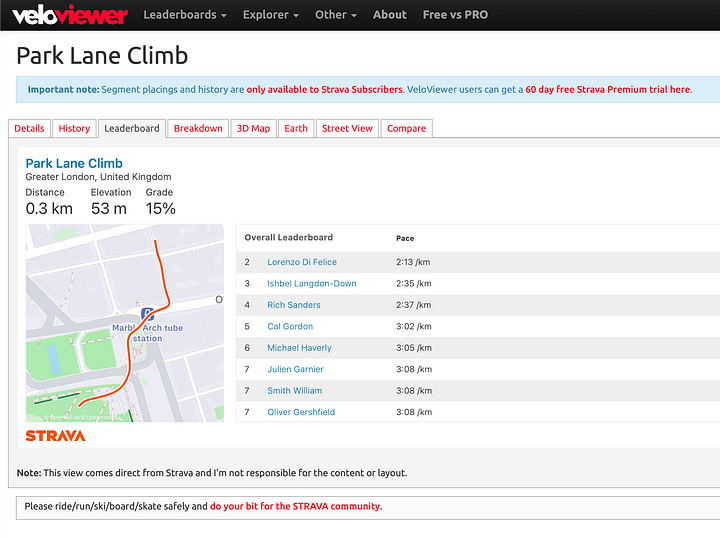
While Strava’s Segment Explorer is now a paid feature, the Doogal interface provides free access to explore individual segments (this may not remain available indefinitely). Segments can be viewed on Veloviewer, which provides track breakdowns and leaderboards showing who has actually run a given route.
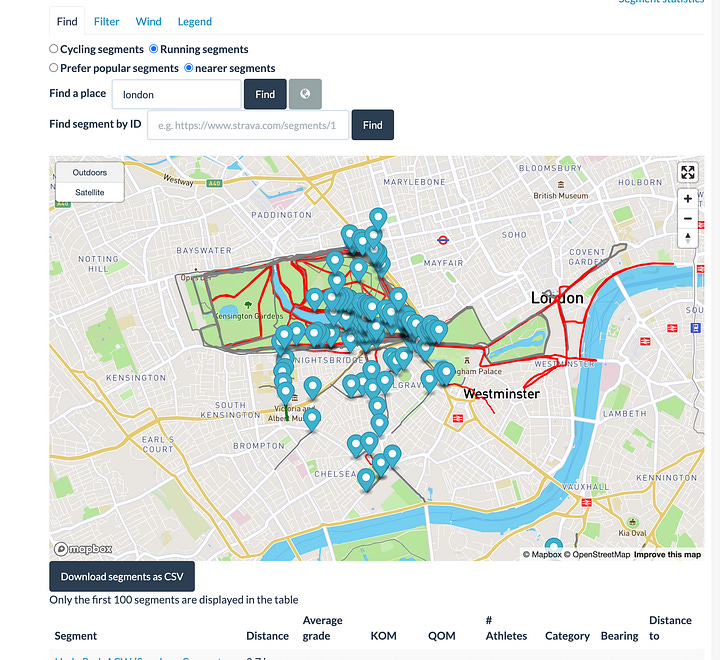
This becomes particularly valuable at airbases and outposts in remote areas. The Mazar-i-Sharif airbase in northern Afghanistan, for example, shows a significant volume of segment data from its period of active use.
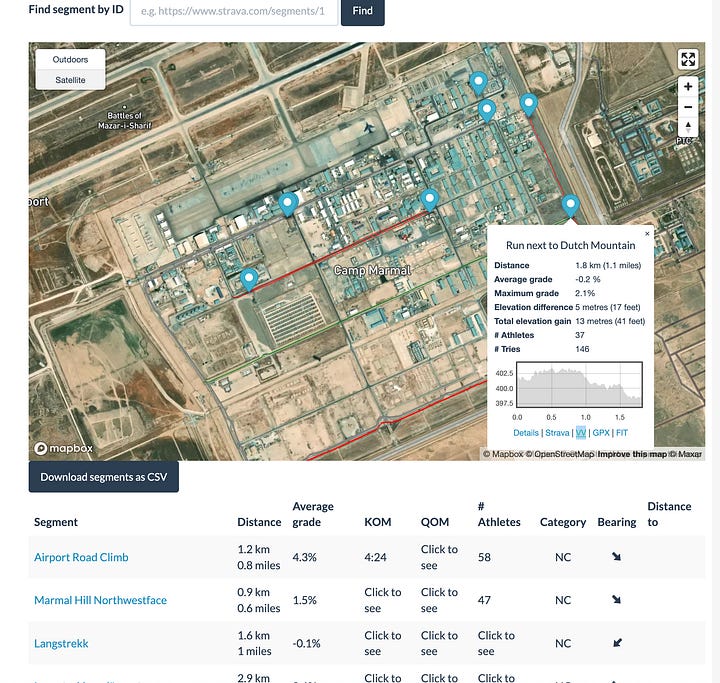
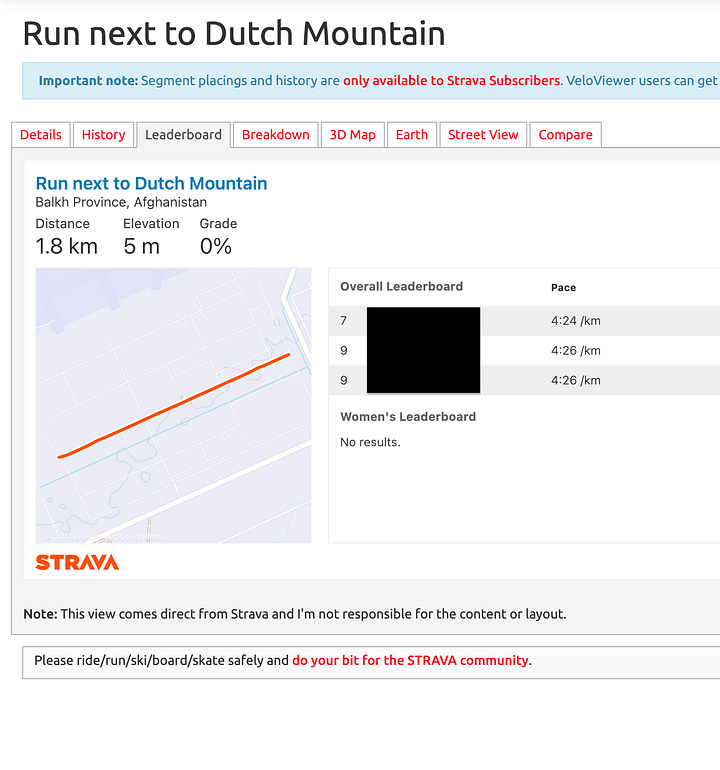
In a 2018 post on Strava’s data availability, I looked at soldiers at Camp Taji in Iraq, Camp Castor in Mali, UN bases in South Sudan, and European oil workers at the In Amenas gas facility in Algeria. Nick Waters (Bellingcat, 2020) identified SAS troops at Hereford using the same method. The i Paper (2026) used the same method to identify 519 UK service personnel at Faslane, Akrotiri, Diego Garcia, Menwith Hill, and Fylingdales in three months of public data.
Technique 3: Cross-platform attribution
Many Strava profiles confirm identity without any specialist tooling. When you come across a name on Strava, check the display name against Google, LinkedIn, and Facebook. Look at the bio for employer, unit, or role. Run the profile photo through reverse image search (Google Lens, Yandex). Check the gear list: a Garmin Tactix suggests military or tactical use; a consumer Forerunner less so. Check followers and Strava Clubs, as some bases and units have unofficial clubs that list all members, making affiliation mapping straightforward.
Le Monde used this process to confirm multiple agents linked to French President Macron, referencing names, photos, and profile details across platforms.
What’s changed since 2018
Many of the techniques seen in past Strava exposure case studies have since been paywalled and some privacy gaps plugged. People have become more aware of how Strava can reveal personal details, including home addresses. That shift in awareness matters.
But these exposures also point to a darker reality: location-sharing through fitness apps can create serious risks, including stalking, intrusion, and runners being targeted on isolated routes, especially in poorly lit areas without CCTV. Those harms are rooted first and foremost in predatory behaviour and broader social problems, but app design and privacy defaults still play an important role in reducing vulnerability. Strava’s default remains public. It has been since launch. The one change that would materially reduce recurrence (making new accounts private by default) remains outstanding.
Further reading:
GIJN / Santiago Villa (April 2025), a comprehensive practitioner guide to Strava
My 2018 Medium piece on the Segment Explorer as an OPSEC risk
Aware Online’s walkthrough of the fake-run/Flyby workflow
NetWatch Global’s case studies on insurance fraud applications
Watches of Espionage on the Swedish PM leak and smartwatch risks
The i Paper research on 519 UK service personnel identified at sensitive sites in 2026.
4. Case File: The Russian Military Men Manning Moscow’s Shadow Fleet
Source: OCCRP, joint with Delfi (Estonia), Helsingin Sanomat (Finland), and iStories (Russia). I’d recommend reading the original in full.
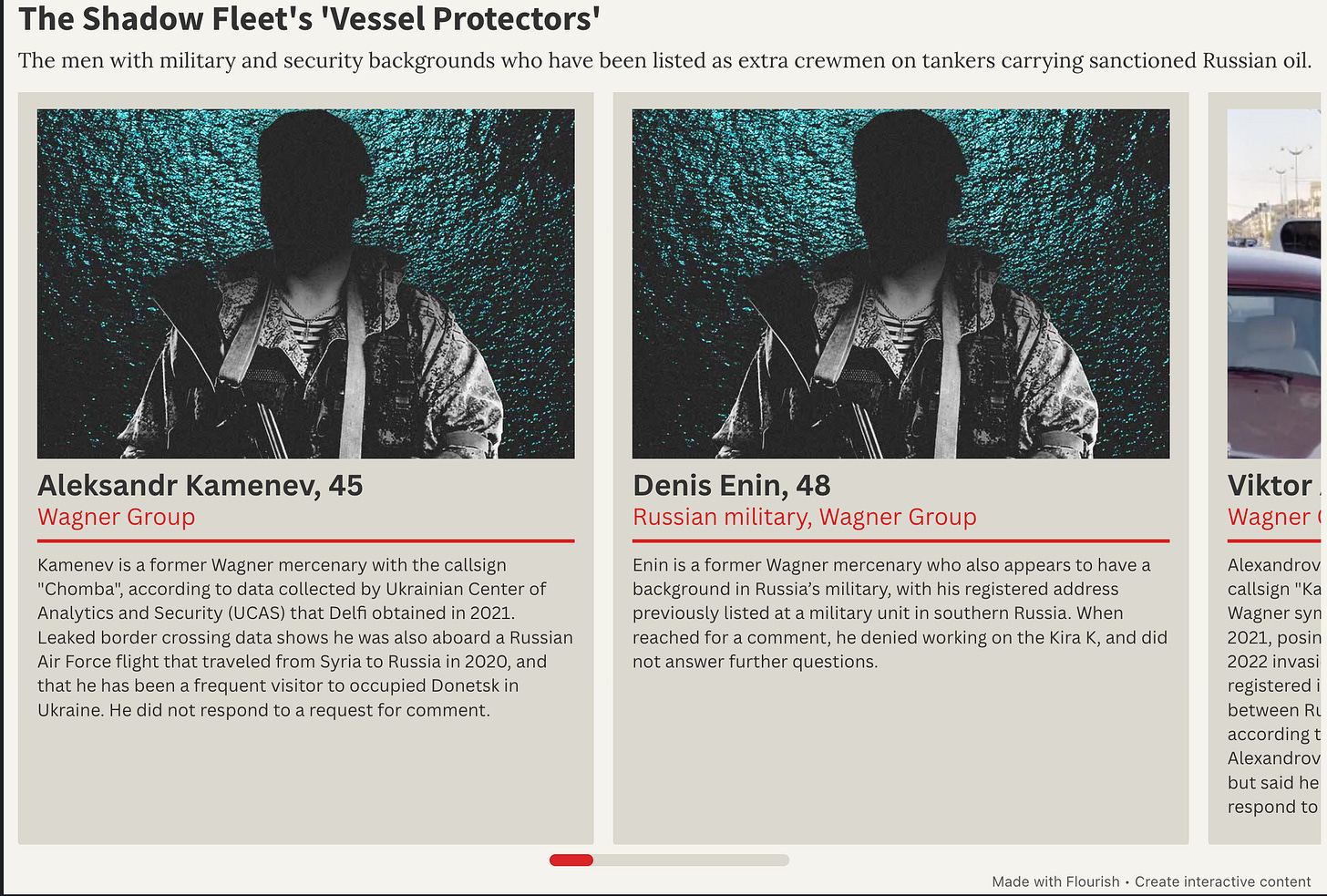
OCCRP identified 17 Russian men without maritime credentials aboard sanctioned oil tankers in the Baltic Sea, 13 of them linked to Wagner Group, GRU military intelligence, or Russian paratrooper units. The men were present as “extra crew” on top of the standard operational complement: two-man “vessel protection teams” deployed on tankers since mid-2025, concentrated on Baltic routes near European maritime enforcement zones. Two named individuals were directly identified and verified: Aleksandr Malakhov, linked to the 22nd Spetsnaz Brigade/GRU, and Viktor Alexandrov, a former Wagner mercenary.
The significance is structural: Russia’s shadow fleet, estimated at over 1,000 vessels, though figures vary by source, has shifted from a sanctions evasion mechanism for oil revenue into something investigators describe as a potential maritime security threat.
The investigation combined four independent data streams:
1. Crew manifest analysis. Reporters obtained crew manifests from sanctioned tankers across 20 journeys. They compared the number of personnel listed against each vessel’s standard operational requirement; surplus personnel without maritime job titles or simply called “technicians” or credentials were flagged.
2. Leaked Wagner mercenary registry. A 2021 leak of internal Wagner Group personnel records, widely circulated among investigative journalists since it emerged, provided a reference database for cross-checking names.
3. Border crossing data. A separate leak of Russian border crossing records allowed reporters to confirm that specific individuals had previously been present in Syria and Russian-occupied Donetsk, consistent with Wagner operational history, not civilian maritime employment.
4. AIS vessel tracking and social media. Standard maritime OSINT, MarineTraffic, VesselFinder, was used to confirm vessel positions and routes. Social media profiling of named individuals produced additional corroborating detail.The methodology in plain terms
The methodology in plain terms
This is a joins-across-databases investigation. The core technique: take a list of names from one source (crew manifests), check them against a second source (leaked military/mercenary registry), and use a third source (border records) to independently verify the connection. None of the three sources alone is sufficient; the convergence of all three is what makes the findings publishable.
The tools that support this kind of research in the maritime sector include Equasis for vessel ownership, management company, and flag state history; GISIS for maritime verification and reference; MarineTraffic and VesselFinder for AIS position history and voyage records; Sayari and OpenCorporates for corporate ownership chains behind management companies; and OCCRP Aleph for cross-searching leaked and public datasets simultaneously.
The leaked databases (Wagner registry, border crossing data) are not publicly available through standard OSINT channels. They circulate among investigative networks and were originally obtained through sources or prior leaks. That’s worth acknowledging: the methodology is reproducible up to the point where leaked primary material becomes the key evidence.
This case file matters for three reasons. It adds a military dimension to the shadow fleet story that most sanctions-focused maritime analysts haven’t been tracking. The methodology is explicit enough to walk through step by step, with database sources named and accessible (except for the leaked registries, which should be flagged as such). And it connects directly to an ongoing story: with European governments debating whether to intercept or board shadow fleet vessels, the presence of Wagner/GRU personnel changes the legal and operational calculus entirely.
Closing Note
I’ve been doing a lot of running lately. Getting back into it ahead of summer, tracking times on the track and building up the gateway into long runs. Like a lot of people this time of year, I’ve been using Strava for it. Logging splits, seeing the route on the map, connecting with others doing the same and finding new tracks.
And then I spent a week writing this edition. A French Navy officer’s morning jog around an aircraft carrier deck. 519 British service personnel (submariners, intelligence analysts, missile warning station engineers) publicly logging runs inside facilities that aren’t meant to be public. Presidential security details mapped across a dozen countries by journalists with a Python script and a sock puppet account. The same app. The same GPS watch on the wrist. The same default setting of public.
Strava is useful for measuring track times. It turns out it’s also useful for tracking aircraft carriers, identifying nuclear submarine crews, and predicting where heads of state will sleep on international trips. The tools we use to share our runs are the same tools investigators use to find things we really shouldn’t be able to publicly see. That’s the thread running through this edition, not just Strava, but the satellite imagery blackout, the shadow fleet militarisation, the coded marketplaces hiding in plain sight on Facebook. Open sources are open in both directions.
If you’ve found this useful, consider becoming a paid subscriber. Every new edition of OSINT Field Notes remains free, that won’t change. But paid subscriptions unlock the full archive of past editions and help me keep doing this work.
Don’t forget to forward this to a colleague who still hasn’t set their Strava to private or wants to find the people who ran the fastest loop of their local park.
Ben.