OSINT Field Notes #8
Phone Data Mercenaries, Stolen Wheat, Hormuz Traffic, and How To Shut Down AdTech Surveillance
Welcome to edition eight of OSINT Field Notes.
It’s been a busy month for movement data.
Conflict Insights Group used phone-location data, Wi-Fi network names, satellite imagery, flight tracking, and open-source reporting to follow Colombian mercenaries from Bogota through Bosaso, Abu Dhabi, and Kufra into El Fasher during the RSF takeover in October. Avi Scharf, with Yörük Işık and Oded Yaron, traced a Russian-flagged bulk carrier called Abinsk into Haifa carrying Ukrainian wheat stolen from occupied territory. CNN visualised the collapse of Strait of Hormuz traffic from around 3,000 vessels a month down to 191 vessels in April.
None of these is a single-source story.
The Case File this month walks through the CIG report on Sudan, one of the clearest examples of phone-derived location data working as a conflict-evidence layer in a live war.
The Technical Teardown is a defensive one this month, written in response to the Case File. The same data pipeline that CIG used can also be purchased by surveillance vendors, private intelligence firms, and repressive states. If you do work that puts you in any kind of risk profile (conflict reporting, hostile-source investigation, exile journalism, work involving authoritarian states), you might be a target for those seeking to use Adtech data for nefarious purposes. The Teardown walks through how to shut that down on iOS and Android.
If you’re finding value in this newsletter, the back catalogue (editions 1–7) is available to paid subscribers. Each new edition stays free. That won’t change. But paid subscriptions help me keep producing this work and give you access to the full archive. You can upgrade on the OSINT Field Notes Substack page.
Ben.
1. DISPATCHES
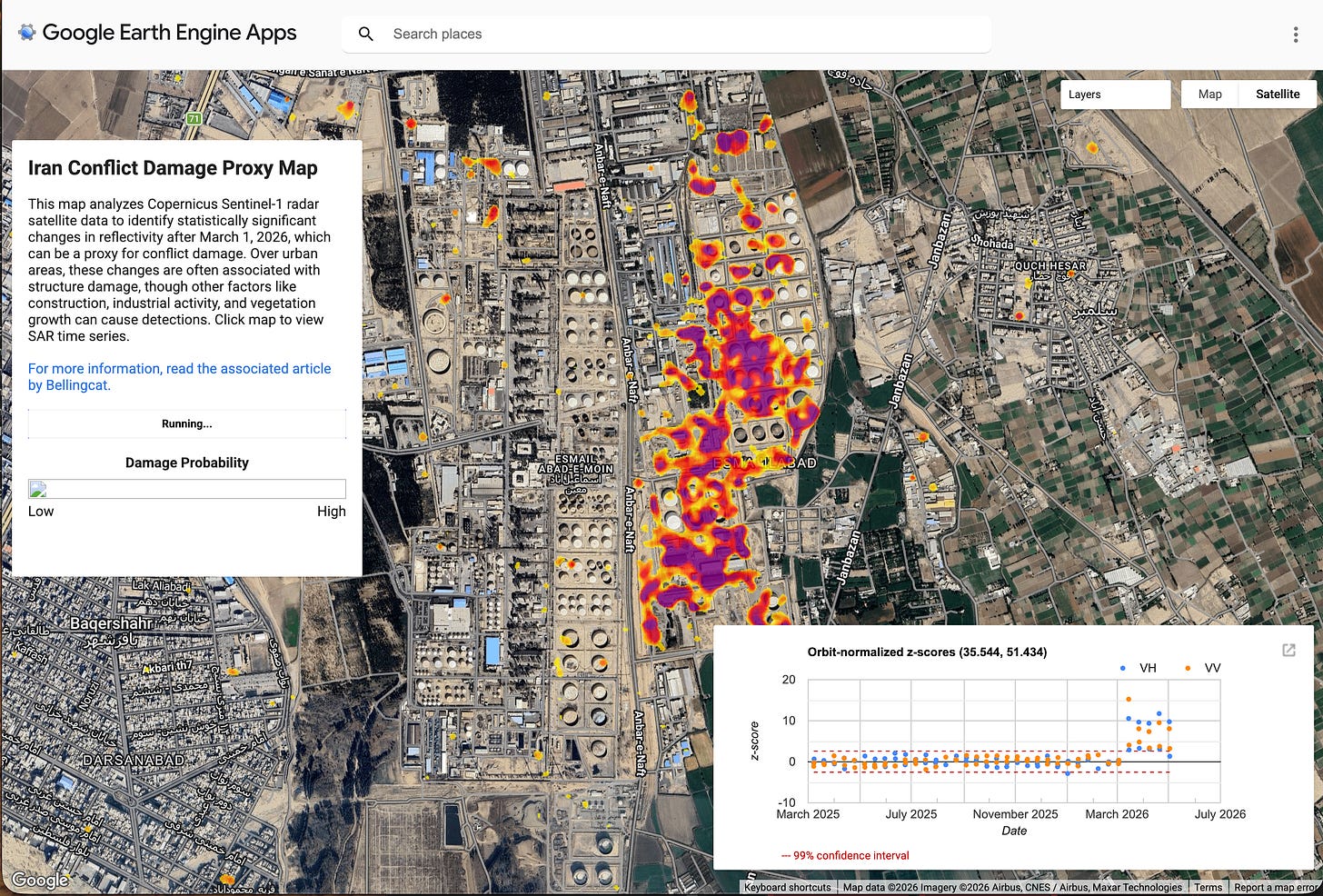
Bellingcat launches an Iran Conflict Damage Proxy Map
Bellingcat released the Iran Conflict Damage Proxy Map on 7 April, an open-source tool built on Sentinel-1 SAR data and the Pixel-Wise T-Test (PWTT) algorithm to detect potential building damage across Iran and the Gulf. It's an updated version of the Gaza Damage Proxy Map first launched in 2023, built specifically because commercial optical imagery is being restricted while ESA's Copernicus programme, which operates Sentinel-1, isn't subject to US government access requests.
Investigator takeaway: Learn one Sentinel-1 workflow before you need it. A crisis is a poor time to start working out what backscatter and orbit direction mean, and the free Copernicus stack is one of the most resilient public options for monitoring through restricted conditions.
Watches of Espionage spots blurred watches in recent DoD photos
Watches of Espionage flagged what appears to be a pattern of smart watches being blurred in official DoD imagery. As they document, smart watches continuously collect GPS, health metrics, communications, and pattern-of-life data, much of which feeds the same AdTech ecosystem as this month’s Case File. In the last edition of OSINT Field Notes I looked at how Strava data from military wearables has repeatedly exposed sensitive personnel and locations; the instinct to redact these devices makes sense.
Investigator takeaway: Wearables leak the same kinds of data that AdTech brokers resell, with extra information attached: vitals, sleep, stride patterns, and continuous location. For sensitive work, the right answer often isn’t a setting toggle but a hardware change.
Russia’s shadow fleet brings stolen Ukrainian wheat into Haifa
A Haaretz investigation by Avi Scharf, with Yörük Işık and Oded Yaron, traces how grain stolen from Russian-occupied Ukrainian territory has been systematically sold into Israel. Haaretz identified at least four shipments unloaded this year, with internal Russian port logs reportedly listing 30+ Israel-destined shipments; the pattern dates to 2023.
Investigator takeaway: Maritime sanctions evasion is rarely a single-source story. AIS gaps, flag changes, bulk-carrier specifications, port call records, and official disclosures all play a role, but the work is in joining them up against a known route. Yörük Işık’s pinned threads on X are one of the most consistent public sources for shadow-fleet pattern analysis.
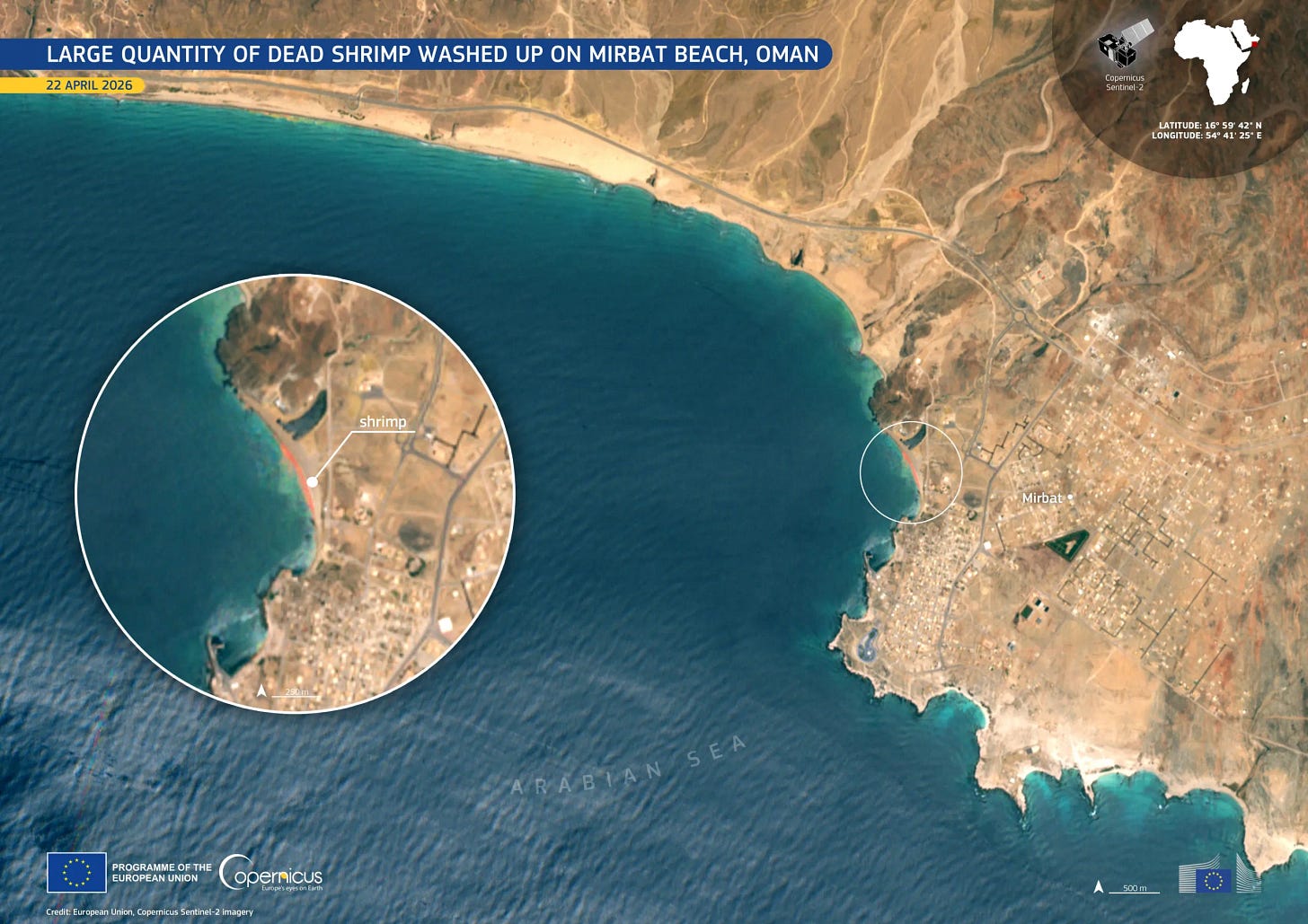
Sentinel-2 picks up a mass shrimp stranding off Oman
Copernicus published a Sentinel-2 image of Mirbat Beach on the south-western coast of Oman as its Image of the Day on 3 May, showing the sand turned visibly pink and red by a mass stranding of dead red shrimp. The image was acquired on 22 April.
Investigator takeaway: Sentinel-2 at 10m picks up coastal and biological events that don’t always show up in conflict-monitoring workflows but matter for environmental investigations and ground-truth verification. Keep coastal phenomena in mind when reviewing claims from coastal locations.
CNN visualises how the Iran war shrank Hormuz traffic
CNN published a visual deep dive on how the Iran war has reshaped shipping in the Persian Gulf and Strait of Hormuz. Before the US and Israeli strikes in late February, around 3,000 vessels passed through monthly; Kpler data shows 191 in April, running at about 5% of pre-war volumes, with oil tanker flows near 15 million barrels per day before the war, roughly a fifth of global oil trade.
Investigator takeaway: Shipping data, transport and trade metrics aren’t just statistics for financial news, but can indicate impact of global events such as war, blockades and other impacts. Open source findings can really supplement some of the on-ground impacts of what trade deficits have.
HRW and Security Force Monitor build an 18-month Burkina Faso atrocity record
Human Rights Watch published None Can Run Away on 2 April, a 316-page report documenting 57 incidents across Burkina Faso between January 2023 and August 2025 that killed at least 1,840 civilians, implicating President Traoré, senior commanders, and JNIM leaders for war crimes and crimes against humanity. The methodology involved 450 interviews combined with large-scale open-source analysis (satellite imagery, video, photo, weapons identification), chain-of-command databases built with Security Force Monitor, and an in-house LLM to triage tens of thousands of videos. Sam Dubberley’s LinkedIn post gives an unusually clear look at the production.
Investigator takeaway: Custom tooling on this scale is increasingly standard for serious human-rights investigations. The pattern (LLM triage of unstructured video and social media, structured chain-of-command databases, geolocation across known incident sites) translates to any long-form documentation project where the volume of visual material outruns what a human team can review.
Public Mali MyMap tracks JNIM and other armed-group base takeovers
I’ve recently been geolocating quite a few bits of footage from Mali, plotting JNIM and other armed-group takeovers of bases and security positions, and have since found an effort to map some of the crowdsourced work here. It’s a lightweight resource of the kind that fills gaps in regions where commercial imagery and major newsroom coverage are sparse.
Investigator takeaway: Worth bookmarking, and worth checking against local reporting and satellite imagery. Lightweight public maps of geolocated content are a useful template for documenting incidents where you want the audience to see a structured layer alongside the narrative. But please credit the volunteer efforts of those that look at shrubs in grainy footage and match them with Google Earth features to get those much-desired coordinates.
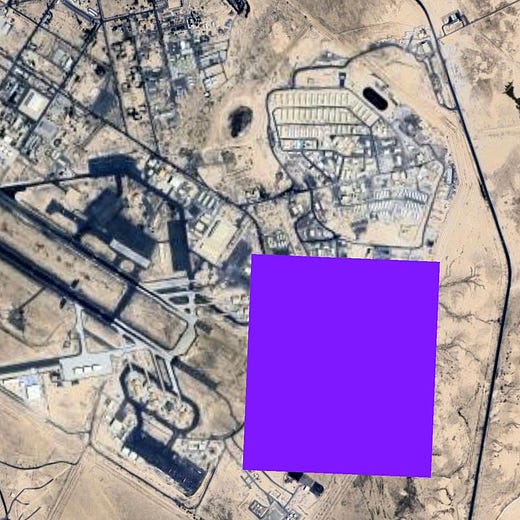
Kuwait blurring as a provider-comparison technique
OSINTtechnical noted that some map providers appear to blur sensitive Kuwaiti sites after strikes during the Iran war, with Ali Al Salem Air Base cited as an example. A closer look at Kuwait shows numerous small Apple Maps blurs around water towers and power stations that aren’t blurred on Google. Blurring removes information, but it also creates it.
Investigator takeaway: Cross-provider comparison is a method, not a curiosity. Google Maps, Google Earth Pro, Apple Maps, Bing, Yandex, Sentinel-2, and historical imagery layers can each show a different version of the same site.
2. TOOLKIT
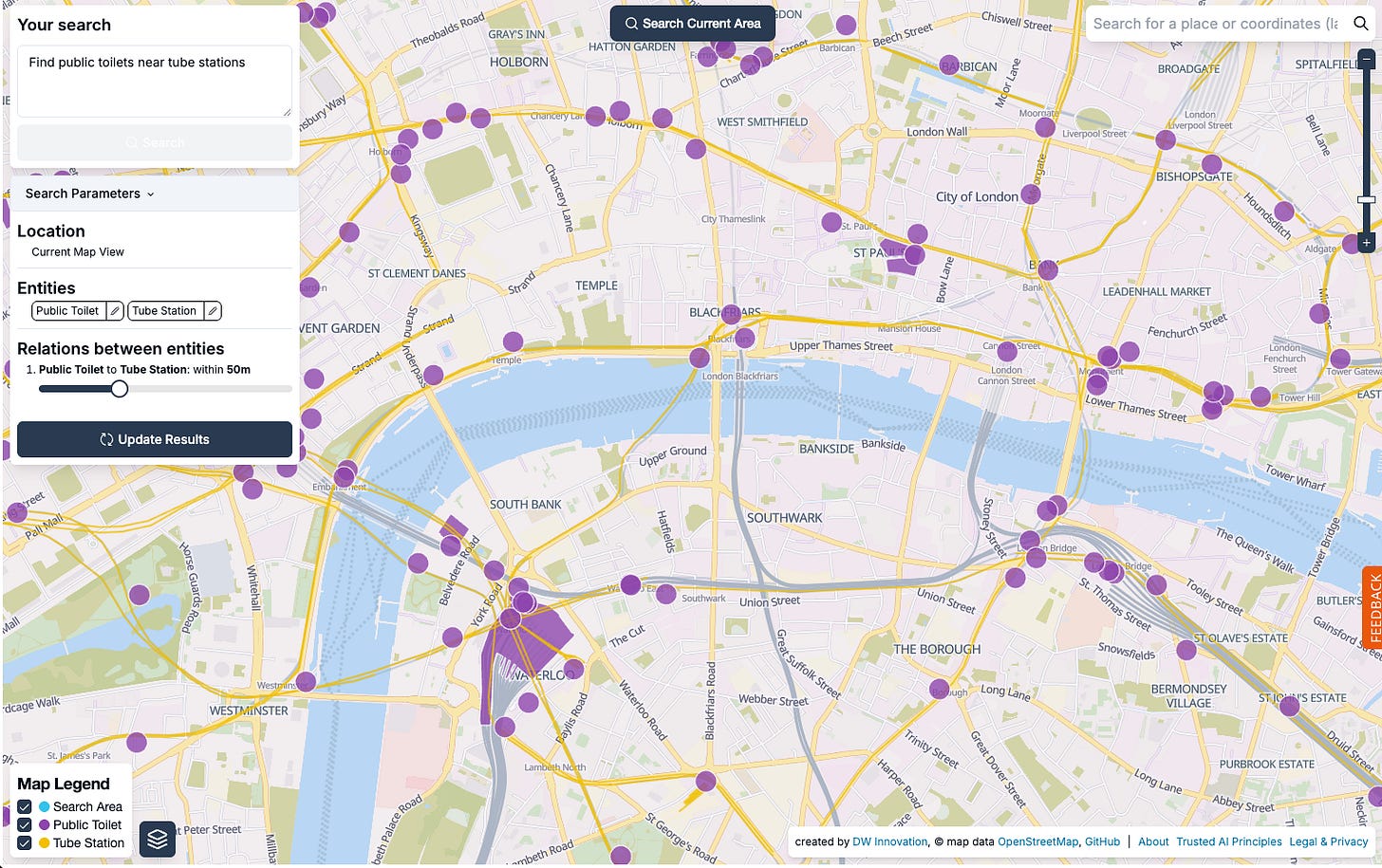
Spot (findthatspot.io): a geospatial OpenStreetMap search tool from DW Innovation that lets you query OSM by entity and relation. Type a natural-language description (features, what’s near what, geographic context) and Spot returns matching candidate locations on a map. Useful for verification, and as a starting point when you have a description but no obvious coordinates. Coverage is only as good as OSM tagging in the area you’re looking at.
Meta Monetization Archive: WHAT TO FIX’s searchable archive of Meta’s own partner-publisher disclosures, backed up since 2019 and released open-source on GitHub. Currently the only such archive because Meta is the only major platform releasing this data. Useful for platform-accountability work, influence-operation research, and tracing how monetisation incentives intersect with harmful content.
Graphify: a GitHub project for turning messy relationship data into graphs. Useful for link analysis when entities, URLs, accounts, companies, devices, domains, or people need to be seen as a network rather than a list. Label edge types clearly (confirmed, alleged, same address, same director, shared phone, co-location, co-occurrence). Graphs make weak links look more confident than they are.
3. TECHNICAL TEARDOWN: PROTECTING YOUR DEVICE FROM ADTECH SURVEILLANCE
The Case File this month (in the next section) shows what advertising-technology location data can do in the hands of an investigator with a public-interest mandate. Conflict Insights Group used it to track Colombian mercenaries from Bogota to El Fasher.
The same data is also sold to surveillance vendors, private intelligence firms, repressive states, and stalkers. The CIG report is a reminder that AdTech location data is operational, not theoretical, and the same tooling that exposes mercenary routes is available to people who target journalists, dissidents, aid workers, and human rights researchers.
This teardown is the defensive companion. It isn’t an OSINT how-to in the usual sense. It’s a settings checklist for keeping your own device out of the AdTech feed. If you read the Case File further down in this newsletter and feel uneasy about your own phone, that’s the right reaction.
The good news is that most of the major exposures can be cut off in twenty minutes of settings work while I will walk through below.
How AdTech location surveillance actually works
The pipeline is straightforward. An app on your phone embeds an advertising SDK (software development kit) from a third party. The SDK collects identifiers, location, and behavioural data, and sends it to the broker’s servers. Brokers aggregate that data across millions of devices and resell access. Some buyers are advertisers. Some are data brokers reselling to other buyers. Some are private intelligence firms. Some are surveillance vendors selling location-tracking products to law-enforcement, intelligence and government customers.
Citizen Lab’s analysis of Penlink’s ad-based geolocation surveillance technology walks through the supply side of this market. The Penlink product is marketed to law enforcement and intelligence customers, and sources its location data from the same advertising ecosystem that funds the apps on your phone.
Two key identifiers worth knowing about:
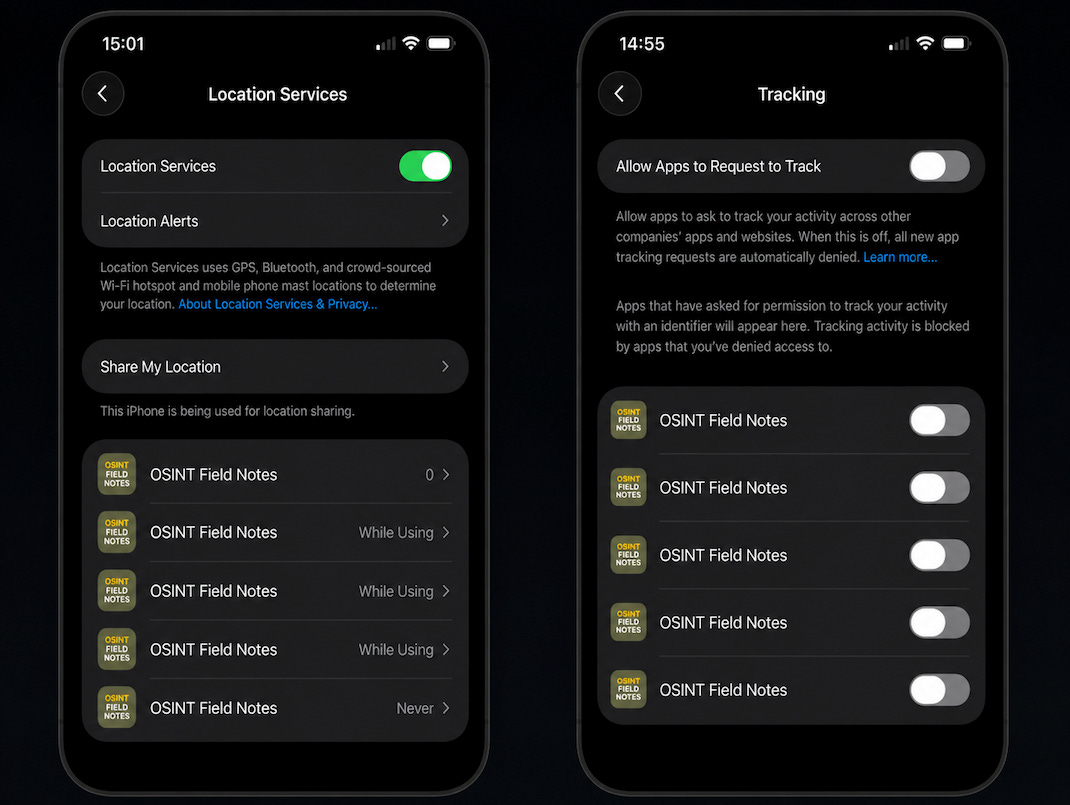
iOS uses IDFA (Identifier for Advertisers). Since iOS 14.5, apps must request permission to track you across other apps and websites under App Tracking Transparency, or ATT. Deny it, and the IDFA is supposed to be unavailable to that app.
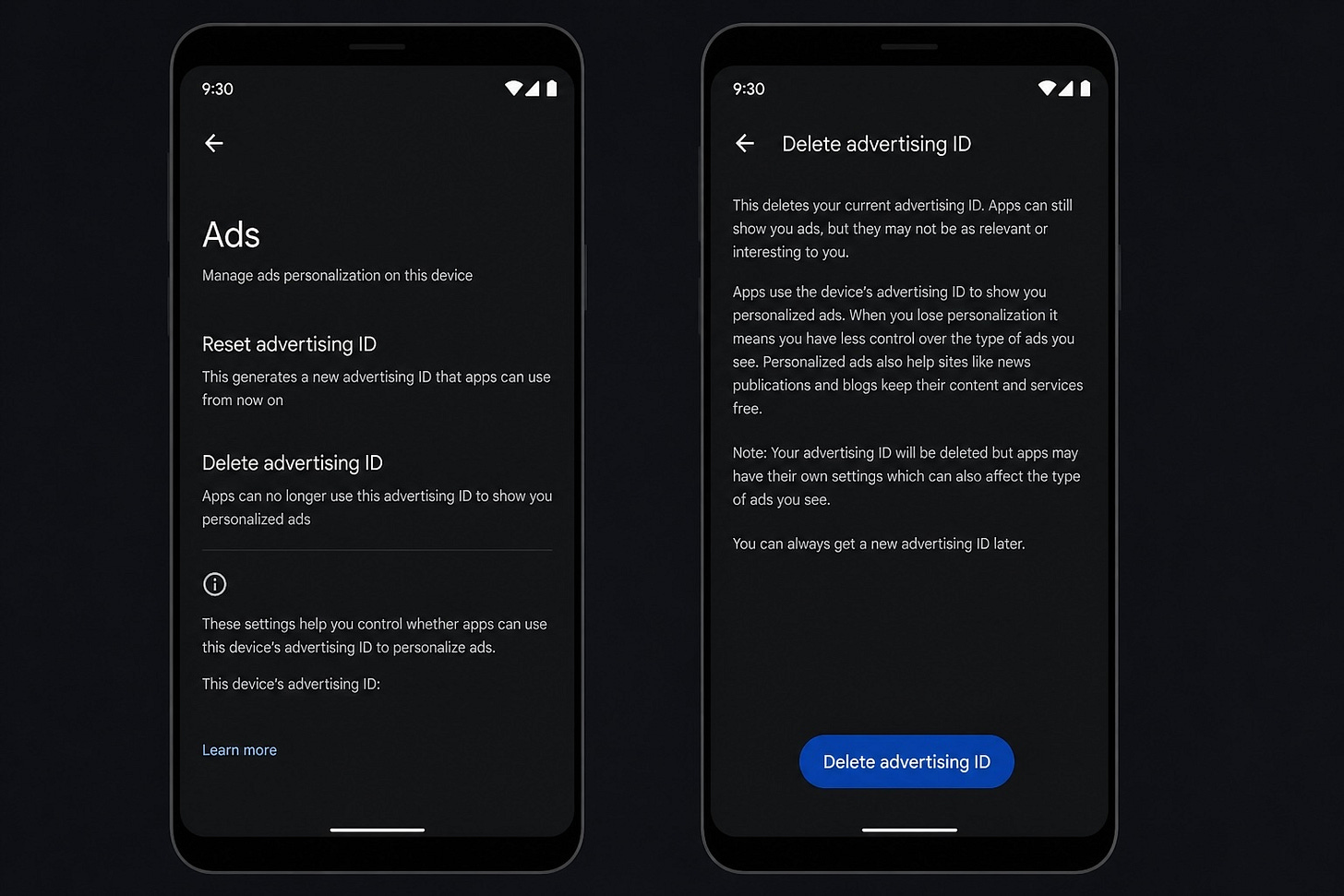
Android uses an advertising ID (sometimes called AAID or GAID). Recent Android versions let you delete the advertising ID outright, which is stronger than just opting out of personalisation.
In addition to advertising IDs, both ecosystems leak data via location permissions, sensor data, IP addresses, Wi-Fi network names, and what Google itself calls “other persistent or proprietary identifiers” that survive even when you delete the advertising ID.
iOS: what to do
Three changes will cover most exposures.
Turn off cross-app tracking globally: Go to Settings, then Privacy & Security, then Tracking. Turn off “Allow Apps to Request to Track” so apps can’t even ask. Apple support note.
Review apps you’ve already granted tracking to. Same screen. Revoke any that don’t strictly need it.
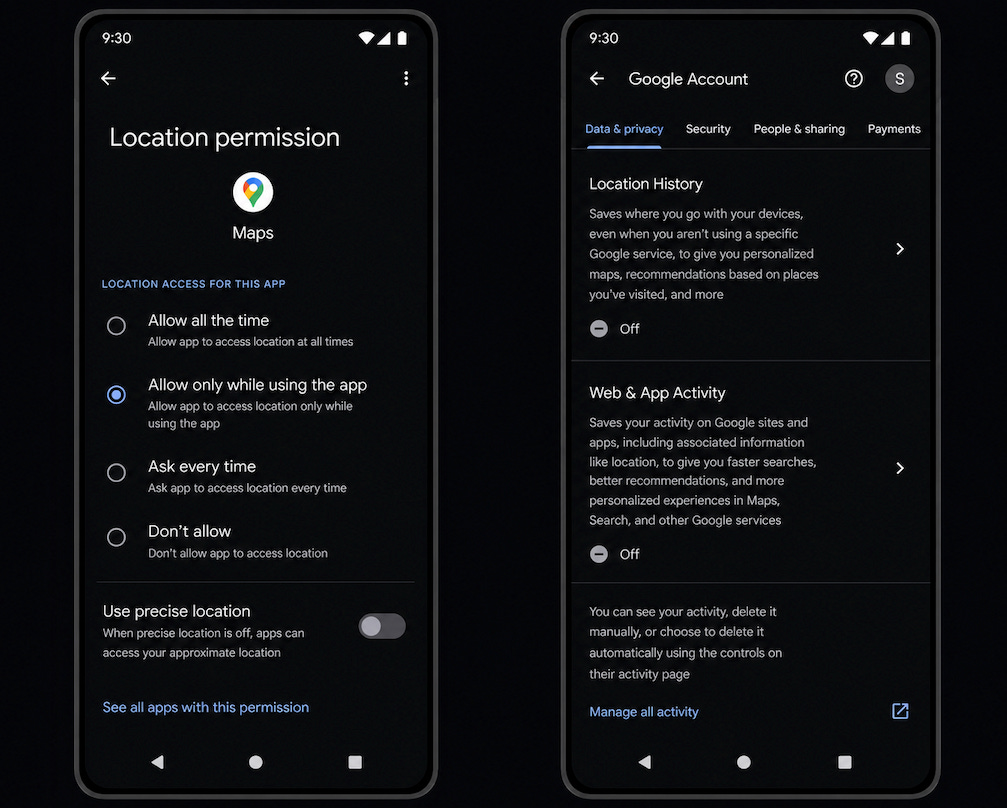
Audit location permissions. Settings, then Privacy & Security, then Location Services. Set apps to “Never” or “While Using” rather than “Always”. Turn off “Precise Location” for any app that doesn’t need street-level accuracy. Apple support note.
Note: ATT (App Tracking Transparency) only exists on iOS 14.5 and later. If you’re on an older device, the protection isn’t available, and that’s a reason to update.
Android: what to do
Delete the advertising ID. On recent versions of Android: go to Settings, then Privacy, then Ads, then Delete advertising ID. On older versions you’ll only see “Opt out of ads personalisation”, which is weaker but better than nothing. California Privacy Protection Agency guide.
Review location permissions. Settings, then Location, then App permissions. Revoke “Allow all the time” for any app that doesn’t strictly need background location.
Turn off Google location history and Web & App Activity if you don’t need them.
Exact menu paths vary by vendor (Samsung, Pixel, Xiaomi, OnePlus all do it slightly differently), but the principles are the same.
Limits of these protections
Settings hygiene is necessary, not sufficient. Three things are worth knowing.
An app can still share data server-to-server if its permissions, privacy policy, consent flow and applicable law allow it, and that sharing may happen independently of the advertising ID setting.
Google notes that deleting the advertising ID does not necessarily stop all app-level tracking, because apps may have their own settings and may use other identifiers, subject to platform policy and law. Apple’s ATT has been the subject of multiple reports suggesting that some apps continue to track despite users denying permission.
Realistically, the strongest defence isn’t a single setting. It’s app minimisation. The fewer apps you have installed, the smaller the ability to track. Audit what’s on your phone. Uninstall anything you don’t actively use. Be especially sceptical of free apps that ask for permissions disproportionate to their function.
For higher-risk profiles
If your work involves conflict reporting, exile journalism, dissident communication, sanctions investigations, or any threat model where state-level adversaries are realistic, consumer-grade settings are a starting point, not an endpoint. Worth looking at:
GrapheneOS for a hardened Android setup, especially if you can tolerate the usability trade-offs and device limitations. Graphene is free and the code is open-sourced.
A separate burner phone for sensitive work, never logged into your main accounts, with as few apps as possible installed.
Network-level monitoring of what your phone is actually sending. Tools like NextDNS let you see which trackers your apps are connecting to.
A VPN to mask IP-derived geolocation, with care taken about VPN provider trust. Note: VPNs do not stop app-level location sharing.
Periodic full-device reset, with only essential apps reinstalled.
Here’s some further resources if you’re after a deeper dive on this:
California Privacy Protection Agency: Limit Mobile App Tracking
Canadian Centre for Cyber Security: Protecting your information when using applications
Privacy International: iOS opt-out guide and Android opt-out guide
Citizen Lab: Analysis of Penlink’s ad-based geolocation surveillance tech
The Case File shows what AdTech data can do for accountability. The Citizen Lab work shows what it can do against people who can’t push back. If your work makes you a target, sacrificing a few minutes of digital safety work each week is well worth it.
4. CASE FILE: PHONE DATA AND THE FALL OF EL FASHER
Source: Conflict Insights Group, Blood Money: How UAE Support and Foreign Mercenaries Enabled the Fall of El Fasher (April 2026). Also covered by the BBC. I’d recommend reading the original in full. What follows focuses on methodology rather than reproducing the report.
Conflict Insights Group tracked more than 50 devices associated with Colombian mercenaries operating in Sudan between 1 April 2025 and 20 January 2026.
The report argues that a UAE-backed network of Colombian mercenaries provided critical military support to the Rapid Support Forces before and during the October 2025 capture of El Fasher, North Darfur. It is reported they flew drones, trained soldiers (including child soldiers, according to multiple sources), and operated as artillerymen and instructors. The network is linked to the Desert Wolves brigade, led by retired Colombian Army Colonel Alvaro Quijano, who is UAE-based and US Treasury-sanctioned. Quijano’s brigade was paid and employed by Global Security Services Group (GSSG), a UAE-based company with documented ties to senior Emirati officials and to Sheikh Tahnoon bin Zayed Al Nahyan’s business network.
The investigation combined six independent data streams.
1. Commercially available advertising-technology (AdTech) data. Anonymised device location data, used only when a second source provided independent confirmation. CIG explicitly says it discarded devices whose location and associated information raised any doubt, and sought secondary opinions on its manual analysis.
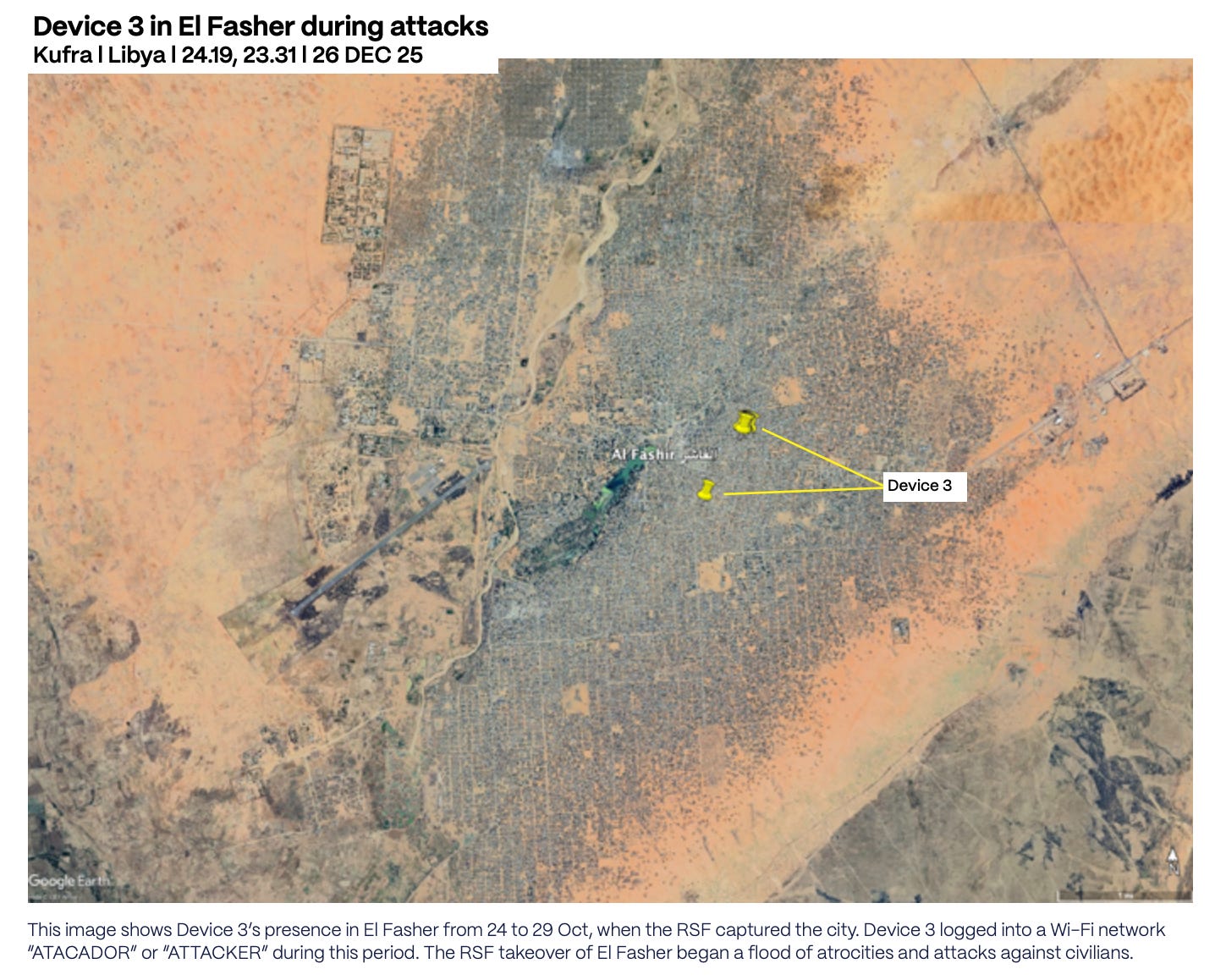
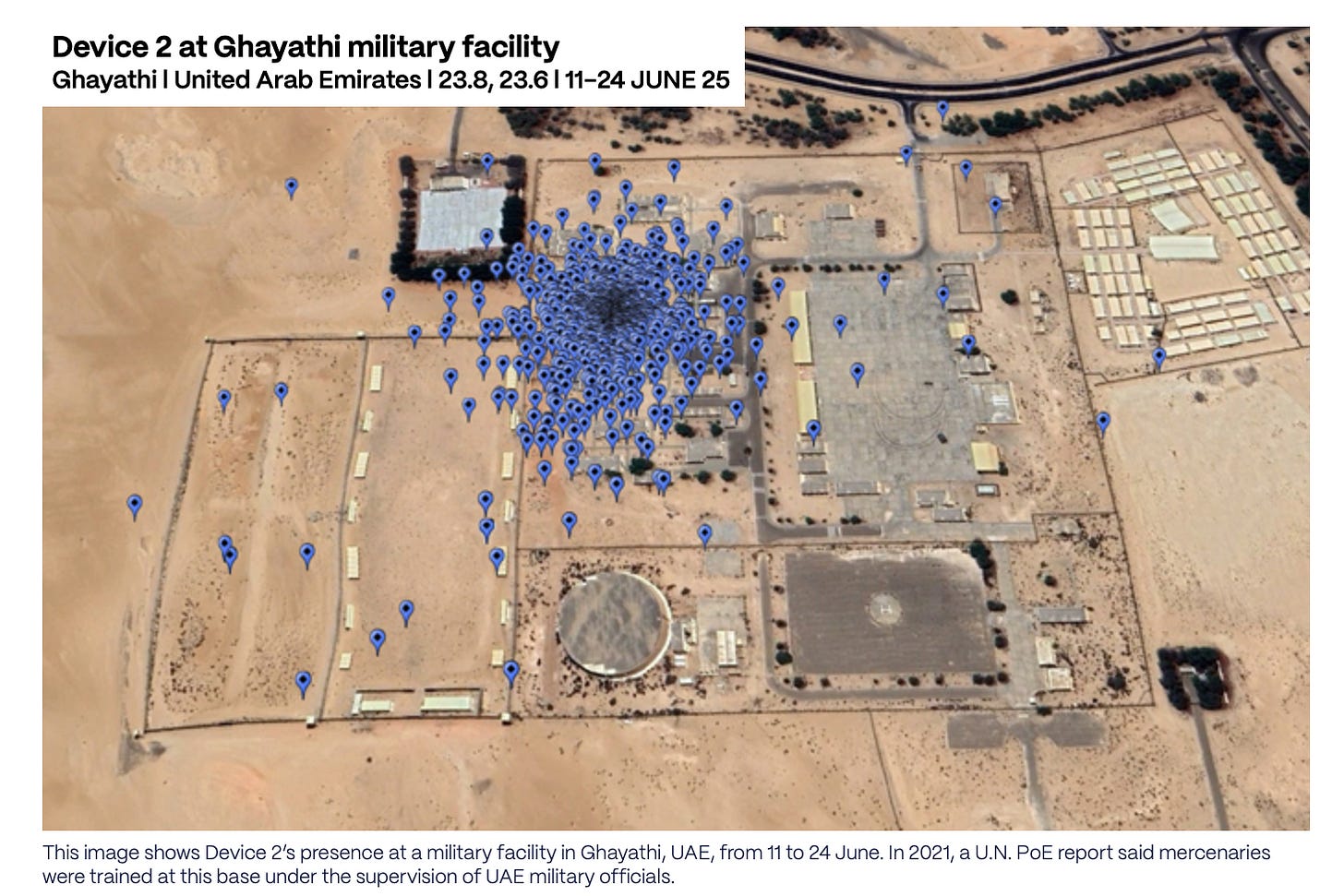
2. Device language settings and Wi-Fi network names. This is the part that turns AdTech from “a phone was here” into something analytically richer. Device 1 connected 14 times to a Wi-Fi network named “DRONES” between 18 April and 14 May 2025, then 8 times to “LOBOS DEL DISIERTO” (a misspelled Spanish form of Desert Wolves) between 9 and 16 June. Device 3, present in northeast El Fasher from 24 to 29 October during the RSF takeover, connected to a Wi-Fi network named “ATACADOR” (Spanish for “attacker”) with language settings configured to Spanish.
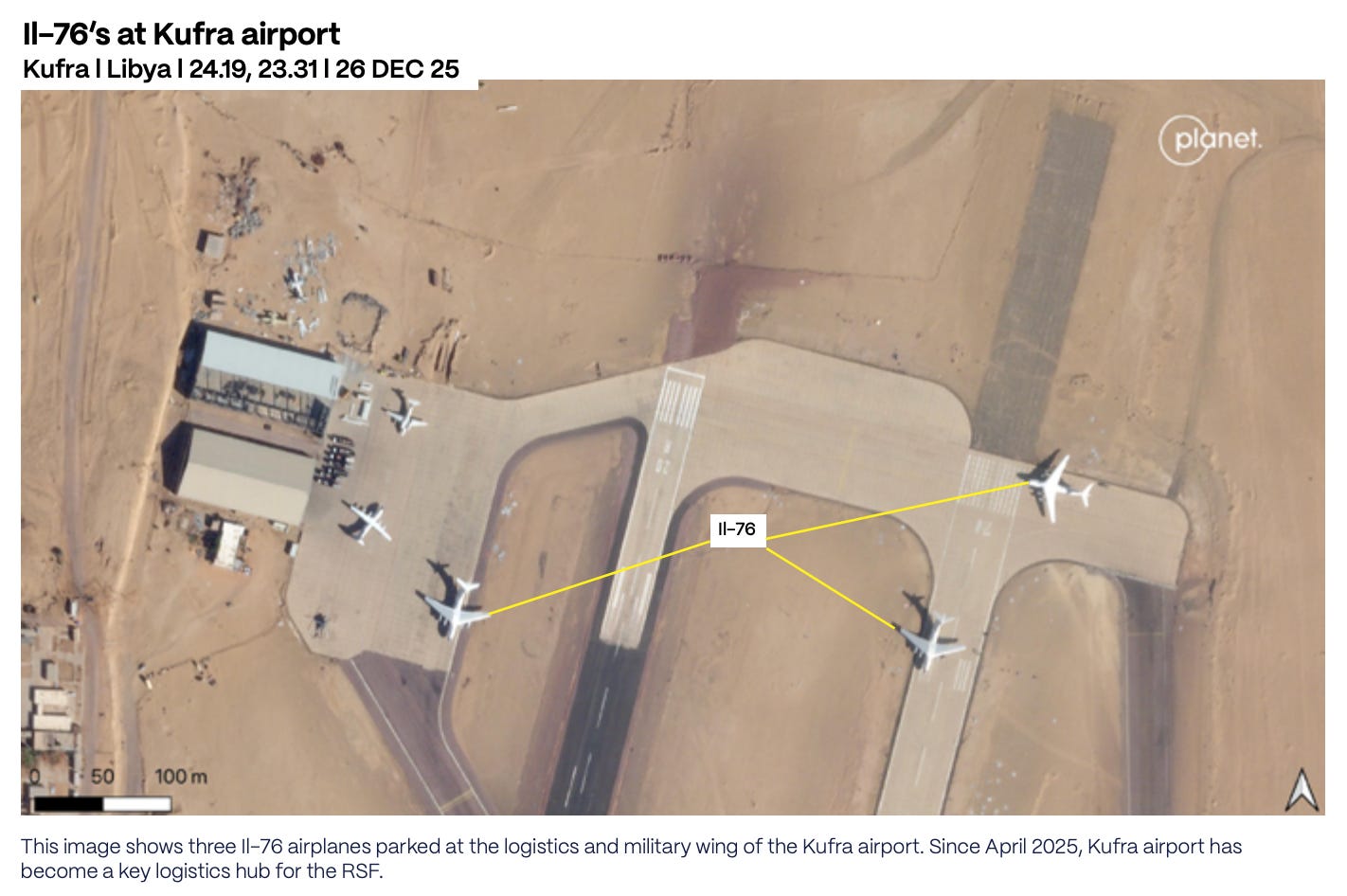
3. Satellite imagery. Used to identify infrastructure consistent with operational claims. A manmade runway around 5.6km from Device 1’s location in remote South Darfur. Weapons-storage facilities at a military barracks in Kufra visited by Device 2.
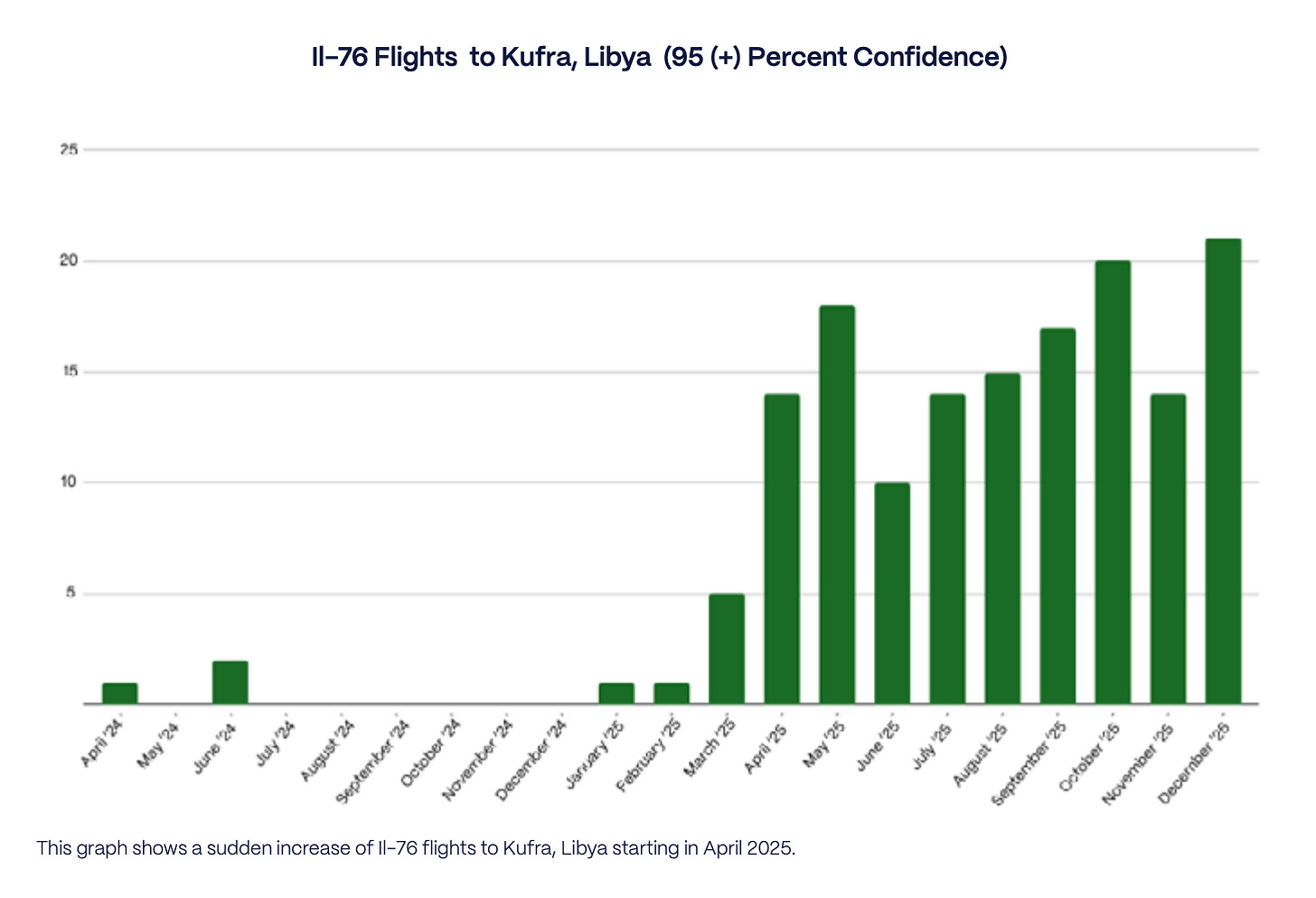
4. Flight-tracking and aircraft pattern analysis. CIG identified 143 Il-76 cargo flights at the logistics or military wing of Kufra airport between 1 April and 31 December 2025, at 95 percent confidence or higher. The same period a year earlier produced just 10. That’s a fourteen-fold increase, and the timing matters. In October 2024, the State Department-funded Conflict Observatory documented Il-76 flights from the UAE delivering weapons to the RSF via Amdjarass, Chad. After that report and the resulting media attention, Amdjarass flights collapsed. Kufra surged from April 2025 onward.
5. Social media videos. Videos geolocated by CIG shows either a Chinese-made CH-95 or FH-95 drone on the Nyala airport runway, with a Spanish-speaking narrator with a Colombian accent. A separate geolocated video from January 2025 shows apparent Colombian fighters in El Fasher using a Serbian M62P10 shell and an M74 mortar.
6. Corporate and sanctions research. CIG notes that GSSG’s CEO, Mohammed Hamdan Alzaabi, shares a name with a Mohammed Hamdan al-Zaabi identified by the New York Times in 2019 as General Manager of Newave, a UAE-based network removed by Meta for coordinated inauthentic behaviour. Unless independently confirmed, that should be treated as a possible identity overlap, not proof that the same person moved from influence operations into mercenary logistics.
The methodology in plain terms
This is a joins-across-sources investigation. CIG took device data and looked for patterns: where the devices were, what language settings they used, what Wi-Fi networks they connected to, how they moved over time. Then it checked those patterns against independent evidence: satellite imagery, airfield activity, Il-76 flights, social videos, sanctions statements, and corporate research.
None of the sources alone is sufficient. The convergence is what makes the findings publishable.
Some of the method is reproducible by most investigators: mapping airports, bases, routes, and logistics hubs; checking satellite imagery for airfield activity; comparing flight patterns over time; geolocating social videos; researching companies and sanctioned individuals; building a timeline from public reporting. Some of it isn’t: the raw AdTech device data, the device-level movement histories, and information withheld for safety reasons. That distinction should be explicit in any case file that depends on controlled-access data, and CIG flags it cleanly.
The atrocity proximity matters. Device 3 was in northeast El Fasher from 24 to 29 October. The RSF captured the city on 26 October. The ICC Prosecutor concluded that war crimes and crimes against humanity took place there. The World Health Organization reported that more than 460 patients were killed by the RSF at the Saudi Maternity Hospital. A US Treasury Department statement of 9 December 2025 says that “supported by Colombian fighters, the RSF captured El Fasher in October 26, 2025.” The phone data doesn’t prove an individual committed a specific crime, and CIG is careful about that. What it does is place devices assessed to be associated with Colombian mercenaries within the operational geography of an atrocity event, alongside independent evidence that Colombian fighters supported the operation.
This case file matters for three reasons:
Phone-derived location data is now a conflict-evidence source in practice, not just in theory.
Foreign-fighter networks can be mapped through movement patterns, not just documents. Phones, airports, Wi-Fi names, language settings, and air cargo movements reveal behaviour that paperwork alone won’t.
The same advertising ecosystem that exposes mercenary routes can also expose civilians, journalists, aid workers, and vulnerable communities. The answer isn’t to pretend the data doesn’t exist. It’s to use it with strict minimisation, corroboration, redaction, and a clear public-interest threshold.
Phone data can reveal the hidden logistics of war. It can also put people at risk.
CLOSING NOTE
I spent most of the past month reading the CIG report and looking into how our devices can seemingly collect pieces of data about us and subsequently be purchased by actors with malign intent.
By the end of it I’d started looking at my own phone differently. Everyone knows by now that phones leak. The difference is in watching a 50-device dataset trace a mercenary brigade from Bogota to Bosaso to Kufra to El Fasher, and realising the plumbing that made that investigation possible is the same plumbing every one of us is plugged into.
The other stories in this edition turn on a similar observation. A ship leaks where it’s docked. A refinery leaks the heat of a strike. A public map collects what few newsrooms have the budget to chase. The leakage is everywhere, and so is the layered, free, public data that turns it into something an investigator can publish.
If you’ve found this useful, consider becoming a paid subscriber. Each new edition of OSINT Field Notes remains free, that won’t change. The full back catalogue (editions 1–7) is now available exclusively to paid subscribers, and supporting the newsletter helps me keep producing the work.
Forward this to a colleague who still thinks phone-location data is only an advertising problem.
Ben.